Abstract
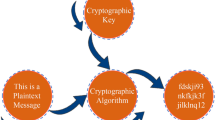
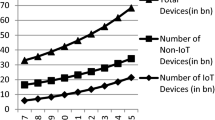
IoT or Internet of Things is a modern term describing the ever growing system of widely interrelated devices which communicate automatically. Almost all devices we consider to be mobile work through an IoT network and participate in this sharing of information. As of late, there has been a rising need to secure communications across smaller, more embedded devices that are increasing in number within IoT networks. These embedded devices may include sensors sending sampled data to a processing unit, or processors themselves that are the brain of a specific embedded device. Securing these systems can be done through cryptography, but standard cryptography is not fully compatible with these small devices. The new constraints presented by securing communications on these devices include minimizing power consumption and resource utilization, while allowing for a viable throughput [Gubbi, Jayavardhana, et al., 2013]. In this paper, a lightweight cryptography algorithm, which attempts to optimize the previously mentioned constraints, is implemented in a system. This implementation was designed using a mix of HDLs (Hardware Description Languages) and designed to be dynamic to be able to accommodate systems with a variety of security requirements. The implementation is applied to a system of sonars that send each other encrypted distance data relative to each other, and use the decrypted data to detect whether they need to adjust their positioning. The aim of using this test system is to emulate use cases in industries where devices must process relative positioning data and communicate securely, while relying on a limited power supply. Examples of these systems include UAVs, drones used for surveillance and recon, etc.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Gubbi, J., et al.: Internet of Things (IoT): a vision, architectural elements, and future directions. Fut. Gener. Comput. Syst. 29(7), 1645–1660 (2013). https://doi.org/10.1016/j.future.2013.01.010
Riou, S.: DryGASCON (2019). https://github.com/sebastien-riou/DryGASCON
Nawir, M., Amir, A., Yaakob, N., Lynn, O.B.: Internet of Things (IoT): taxonomy of security attacks. In: 2016 3rd International Conference on Electronic Design (ICED), Phuket, pp. 321–326 (2016). https://doi.org/10.1109/ICED.2016.7804660
Bertoni, G., Daemen, J., Peeters, M., Van Assche, G.: Duplexing the sponge: single-pass authenticated encryption and other applications. In: Selected Areas in Cryptography. Lecture Notes in Computer Science, pp. 320–337 (2012). https://doi.org/10.1007/978-3-642-28496-0_19
Schlëffer, M.: ASCON v1.2 (2018). https://github.com/ascon
Okamura, T.: Lightweight cryptography applicable to various IoT devices. NEC. www.nec.com/en/global/techrep/journal/g17/n01/170114.html
Parelkar, M.M.: Authenticated encryption in hardware. Ph.D. disssertation, George Mason University (2005)
Muehlberghuber, M., Keller, C., Gürkaynak, F.K., Felber, N.: FPGA-based highspeed authenticated encryption system. In: 20th International Conference on Very Large Scale Integration (VLSI-SoC), Santa Cruz, CA, United States, pp. 1–20 (August 2012). https://doi.org/10.1007/978-3-642-45073-0_1. https://hal.inria.fr/hal-01456959
Khairallah, M., Chattopadhyay, A., Peyrin, T.: Looting the LUTs: FPGA optimization of AES and AES-like ciphers for authenticated encryption. In: International Conference on Cryptology in India, pp. 282–301. Springer, Cham (2017)
Mancillas-López, C., Chakraborty, D., Rodríguez-Henríquez, F.: Reconfigurable hardware implementations of tweakable enciphering schemes. IEEE Trans. Comput. 59(11), 1547–1561 (2010)
Koteshwara, S, Das, A., Parhi, K.K.: FPGA implementation and comparison of AES-GCM and Deoxys authenticated encryption schemes. In: 2017 IEEE International Symposium on Circuits and Systems: From Dreams to Innovation (Conference Proceedings), ISCAS 2017, Baltimore, United States, 28 May 17. Institute of Electrical and Electronics Engineers Inc. (2017). https://doi.org/10.1109/ISCAS.2017.8050315
Deshpande, S., Gaj, K.: Analysis and inner-round pipelined implementation of selected parallelizable CAESAR competition candidates. In: 2017 Euromicro Conference on Digital System Design (DSD), pp. 274–282. IEEE (2017)
Kaps, J.-P., Diehl, W., Tempelmeier, M., Farahmand, F., Homsirikamol, E., Gaj, K.: A comprehensive framework for fair and efficient benchmarking of hardware implementations of lightweight cryptography
López-Trejo, E., Rodríguez-Henríquez, F., Díaz-Pérez, A.: An FPGA implementation of CCM mode using AES. In: International Conference on Information Security and Cryptology, pp. 322–334. Springer, Heidelberg (2005)
Acknowledgment
This research was supported in part by the Air Force Research Laboratory Academy Center for Cyberspace Research (ACCR) Directorate, through the Air Force Office of Scientific Research Summer Faculty Fellowship Program®, Contract Numbers FA8750-15-0-6003 and FA9550-15-0001. Moreover, the IBM-ILLINOIS Center for Cognitive Computing Systems Research (C3SR) - a member of the IBM Cognitive Horizon Network, and the Applications Driving Architectures (ADA) Research Center - one of the JUMP Centers co-sponsored by SRC and DARPA. The authors are grateful to **linx, Inc. and **linx Development Corp. for donations which made work on some of the aspects of the RECO-DryGASCON processor possible.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2021 Springer Nature Switzerland AG
About this paper
Cite this paper
Herndon, R., El-Issa, R., Heer, D., **ong, J., Hwu, WM., El-Hadedy, M. (2021). RECO-DryGASCON: Re-configurable Lightweight DryGASCON Engine. In: Arai, K., Kapoor, S., Bhatia, R. (eds) Proceedings of the Future Technologies Conference (FTC) 2020, Volume 3. FTC 2020. Advances in Intelligent Systems and Computing, vol 1290. Springer, Cham. https://doi.org/10.1007/978-3-030-63092-8_47
Download citation
DOI: https://doi.org/10.1007/978-3-030-63092-8_47
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-63091-1
Online ISBN: 978-3-030-63092-8
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)