Abstract
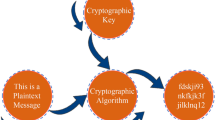
Cryptographic standards were created with the goal of being able to work on a wide range of systems. Small computing systems with limited capacity to implement cryptography have become more popular in recent years. Their performance may not be suitable to fit inside the restricted resources of constricted situations.In order to provide a strategy for the standardisation and security of lightweight cryptographic algorithms, a lightweight cryptography is required. The purpose of this proposed research paper is to standardize lightweight cryptography techniques and security.The Internet of Things, cyber-physical systems, automotive systems, distributed control systems, sensor networks, healthcare and smart grid are merely a few among the new industries where extremely restricted components are networked and working together to achieve a purpose. Many cryptographic methods cannot be implemented in the restricted devices utilized by these apps since the bulk of recent cryptographic techniques were intended for desktop/server settings. When present algorithms are developed to fit into confined settings’ limited resources, their performance may be unacceptable. The suggested research has been created to explore the challenges and then build a plan for the standardization of lightweight cryptographic algorithms and security in light of the aforementioned limitation. While lightweight cryptography is mainly aimed at devices at the low end of the device spectrum, it is crucial to highlight that lightweight algorithms may also be required at the high end. This research therefore suggests a comprehensive lightweight security micro-architecture that combines lightweight cryptography to earn secrecy, lightweight cryptographic hash for authentication of messages, lightweight ID-based encryption for the authentication of entity process, and lightweight protocols for implementing each one of these algorithms in a common micro-architecture that can be used for IoT and embedded/FPGA security.






Similar content being viewed by others
Data Availability
The corresponding author will provide the dataset created during and/or processed during the current investigation upon reasonable request.
References
Sayadi H, Wang H, Miari T, Makrani HM, Aliasgari M, Rafatirad S et al (2020) Recent advancements in microarchitectural security: Review of machine learning countermeasures. In: 2020 IEEE 63rd International Midwest Symposium on Circuits and Systems (MWSCAS). 949– 952
Peng SL, Pal S, Huang L (2020) Principles of internet of things (IoT) ecosystem: Insight paradigm. Springer
Dofe J, Frey J, Yu Q (2016) Hardware security assurance in emerging IoT applications. In: 2016 IEEE International Symposium on Circuits and Systems (ISCAS). 2050–2053
Karam R, Hoque T, Ray S, Tehranipoor M, Bhunia S (2017) MUTARCH: Architectural diversity for FPGA device and IP security. In: 2017 22nd Asia and South Pacific Design Automation Conference (ASP-DAC). IEEE: 611–616
Singh A, Tiwari V, Tentu AN (2023) Authenticated key agreement scheme for IoT networks exploiting lightweight linear algebraic computations. Int J Inf Technol 15(4):1803–1811
Tripathy BK, Jena SK, Reddy V, Das S, Panda SK (2021) A novel communication framework between MANET and WSN in IoT based smart environment. Int J Inf Technol 13:921–931
Kalnoor G & Gowrishankar S (2021). A model for intrusion detection system using hidden Markov and variational Bayesian model for IoT based wireless sensor network. Int J Inf Technol. 1-13
NISTIR D (2016) 8114 Report on Lightweight Cryptography Kerry A. McKay Larry Bassham Meltem Sönmez Turan Nicky Mouha NIST
Sudha KS & Jeyanthi N (2022). Similarity learning-based supervised discrete hash signature scheme for authentication of smart home scenario. Int J Inf Technol, 1-13
Colombier B, Bossuet L (2014) Survey of hardware protection of design data for integrated circuits and intellectual properties. IET Comput Digit Tech 8(6):274–287
Mödersheim S, Viganò L (2019) Alpha-beta privacy. ACM Trans Priv Secur (TOPS) 22(1):1–35
Rupp A, Baldimtsi F, Hinterwälder G, Paar C (2015) Cryptographic theory meets practice: efficient and privacy-preserving payments for public transport. ACM Trans Inf Syst Secur (TISSEC) 17(3):1–31
Noorman J, Bulck JV, Mühlberg JT, Piessens F, Maene P, Preneel B et al (2017) Sancus 2.0: a low-cost security architecture for IoT devices. ACM Trans Priv Secur (TOPS) 20(3):1–33
Ashibani Y, Mahmoud QH (2017) Cyber physical systems security: analysis, challenges and solutions. Comput Secur 68:81–97
Waraga OA, Bettayeb M, Nasir Q, Talib MA (2020) Design and implementation of automated IoT security testbed. Comput Secur 88:101648
Schmitz C, Pape S (2020) LiSRA: lightweight security risk assessment for decision support in information security. Comput Secur 90:101656
Neisse R, Steri G, Fovino IN, Baldini G (2015) SecKit: a model-based security toolkit for the internet of things. Comput Secur 54:60–76
Arora U, Singh N (2021) IoT application modules placement in heterogeneous fog-cloud infrastructure. Int J Inf Technol 13(5):1975–1982
Yu J, Hsiung L, Hajj ME, Fletcher CW (2020) Creating Foundations for Secure Microarchitectures with Data-Oblivious ISA Extensions. IEEE Micro. 40(3)
Evesti A, Pantsar-Syvaniemi S (2010) Towards micro architecture for security adaptation. In: ECSA’10: Proceedings of the fourth European conference on software architecture.181-188
Harsha P (2017) A Novel Micro-Architecture using a Simplified Logistic Map for Embedded Security. IEEE Embed Syst Lett 9(2):41–44
Kgil TH, Falk L, Mudge TN (2005) Chiplock: support for secure microarchitectures. ACM SIGARCH Comput Archit News 33(1):134–143
Author information
Authors and Affiliations
Contributions
The study’s idea, data collection, analysis and interpretation of results, and paper preparation are all confirmed as being the authors’ responsibility.
Corresponding author
Ethics declarations
Conflict of interest
Each author attests that they are not connected to or a part of any group or organisation that has a financial or non-financial stake in the topics or materials contained within this text.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Chakraborty, R., Mondal, U.K., Debnath, A. et al. Lightweight micro-architecture for IoT & FPGA security. Int. j. inf. tecnol. 15, 3899–3905 (2023). https://doi.org/10.1007/s41870-023-01460-y
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s41870-023-01460-y