Search
Search Results
-
Human-centred cyber secure software engineering
Software runs our modern day lives: our shop**, our transport and our medical devices. Hence, no citizen can escape the consequences of poor...

-
Secure and trustworthiness IoT systems: investigations and literature review
Internet of Things (IoT) is creating a new automated environment where human interaction is limited, in which smart-physical objects obtain the power...

-
Defining a Secure Software Process
Many organizations take the view that features are the most important delivery and with limited time and resources, this becomes the focus. At the...
-
A Distributed and Secure Software Architecture Based on Blockchain Technology for Application Software
The use of IoT technology is constantly and uninterruptedly increasing. Sensors in the IoT environment collect large amounts of data and send them to...

-
Secure image transmission through LTE wireless communications systems
Secure transmission of images over wireless communications systems can be done using RSA, the most known and efficient cryptographic algorithm, and...

-
Design and Development of Secure Data Transfer Modules in Industrial Control Systems
Industrial control systems (ICS) like supervisory control and data acquisition (SCADA) systems play a crucial role in monitoring and controlling...

-
Periodic event-triggered secure consensus for networked mechanical systems under Denial-of-Service attacks
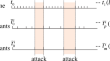
This paper concentrates on the secure consensus problem of networked mechanical/Euler–Lagrange systems. First, a new periodic event-triggered (PET)...
-
Semi-blind AF transmission in secure NOMA systems
In the wireless channel state information (CSI)-assisted amplify-and-forward (AF) networks, an instantaneous CSI of the first hop is required to...

-
Safe Software and Secure Software
In most cyber-physical systems, the functionality is implemented in software. Therefore, the software is responsible for a significant part of safety...
-
Enabling Secure and Efficient Sharing of Accelerators in Expeditionary Systems
The addition of FPGAs in the cloud is an emerging effort to support acceleration and performance with the flexibility of logic reprogramming. The...

-
ARM TrustZone and Secure Operating Systems
This chapter covers ARM TrustZone technology and secure operating systems. It first describes the ARM TrustZone technology as a security extension in...
-
Planning for Secure Software Requirements and Design with UML
It is not possible to build an excellent software product quickly without understanding the requirements. It is known in the security world (and...
-
Secure Communications with THz Reconfigurable Intelligent Surfaces and Deep Learning in 6G Systems
In anticipation of the 6G era, this paper explores the integration of terahertz (THz) communications with Reconfigurable Intelligent Surfaces (RIS)...

-
Secure privacy-enhanced fast authentication and key management for IoMT-enabled smart healthcare systems
The smart healthcare system advancements have introduced the Internet of Things, enabling technologies to improve the quality of medical services....

-
Abstract security patterns and the design of secure systems
During the initial stages of software development, the primary goal is to define precise and detailed requirements without concern for software...

-
State of the Art in Secure Software Systems Development
In the last decades, various concepts have been developed to support the development and maintenance of secure software systems. On the level of...
-
A lightweight, efficient, and secure identity-based authentication scheme for underwater green transport systems
The underwater green transport system ( UwGTs ) is a network of connected, intelligent underwater sensors or Internet of Things (IoT) devices. The...

-
Develop and Maintain Secure Systems and Software
Statistically speaking, a significant number of data breaches have been caused by flaws in applications and by the hackers who attempted to exploit...
-
An Intelligent Blockchain-based Secure Link Failure Recovery Framework for Software-defined Internet-of-Things
The frequency of link failures in Internet-of-Things (IoT) network are more than the node failures. Hence, effective link recovery schemes are...
-
Weight Estimation and Secure Control for Discrete Stochastic Distribution Control Systems Under Sparse Sensor Attacks
In this paper, we investigate the problem of weight estimation and secure control for discrete stochastic distribution control (SDC) systems under...
