Search
Search Results
-
Review of Quantum Image Processing
As an interdisciplinary between quantum computing and image processing, quantum image processing provides more possibilities for image processing due...

-
The State of the Art in Quality Infrastructure Data
The interest in quality infrastructure (QI) has increased significantly over the last decade among researchers, practitioners, policymakers, and...
-
Untangling E-Voting Platform for Secure and Enhanced Voting Using Blockchain Technology
In any country or organization where an election takes place, the voting procedure plays the most vital role. It must be secure and transparent at...
-
A survey on predictions of cyber-attacks utilizing real-time twitter tracing recognition
In recent years, the number of cyber-attacks increased affecting different application types and targets. Many studies tried to focus on proposing...

-
The Big Picture—Information Technology in Enterprises
The term “information technology (IT)” comes with two meanings today: firstly, the original meaning in terms of tools and applications which create,...
-
Application of Big Data Analytics and Internet of Medical Things (IoMT) in Healthcare with View of Explainable Artificial Intelligence: A Survey
The integration of Big Data Analytics (BDA) and the Internet of Medical Things (IoMT) has brought a significant transformation in the healthcare...
-
Map** Risk Assessment Strategy for COVID-19 Mobile Apps’ Vulnerabilities
Recent innovations in mobile technologies are playing an important and vital role in combating the COVID-19 pandemic. While mobile apps’...
-
Deep Learning-Based Automated Learning Environment Using Smart Data to Improve Corporate Marketing, Business Strategies, Fraud Detection in Financial Services, and Financial Time Series Forecasting
The automated learning environment is based on recurrent neural network trained with long short-term memory, used because of its ability to learn, in...
-
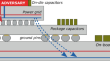
Instruction-Level Power Side-Channel Leakage Evaluation of Soft-Core CPUs on Shared FPGAs
Side-channel disassembly attacks recover CPU instructions from power or electromagnetic side-channel traces measured during code execution. These...
-
An Efficient Group-based Service Authentication and Session Key Negotiation Scheme for mMTC Devices in 5G
With the development of the telecommunication network, the core network is about to enter the era of 5G. 5G is considered an indispensable piece of...

-
Soft Computing and Machine Learning Techniques for e-Health Data Analytics
Medical diagnosis has been a vital part of the healthcare system. The role of computer aided systems is important to identify the exact diseases by...
-
Group signature with time-bound keys and unforgeability of expiry time for smart cities
Internet of Things (IoT) lays the foundation for the various applications in smart cities, yet resource-constrained IoT devices are prone to suffer...

-
Imposing Security and Privacy in the Healthcare Industry Using Blockchain Technology
Blockchain is a leading central concept, and it is gaining more attention in various businesses and various scenarios. It has been one of the...
-
A Review on the Effectiveness of Machine Learning and Deep Learning Algorithms for Collaborative Robot
More and more, we may expect to see robots working side by side with humans as technology advances. Collaborative robot (cobot) is a methodology that...

-
Dual-layer security of image steganography based on IDEA and LSBG algorithm in the cloud environment
The architecture development of cloud computing technology is growing tremendously in recent times, which leads to improvement of scalability,...

-
Introducing robust reachability
We introduce a new property called robust reachability which refines the standard notion of reachability in order to take replicability into account....

-
Diabetes and hypertension MobileHealth systems: a review of general challenges and advancements
Mobile health (mHealth) systems are sip** into more and more healthcare functions with self-management being the foremost modus operandi. However,...

-
Data distribution and secure data transmission using IANFIS and MECC in IoT
IoT entities amass a massive quantity of sensing data and transmit it to the cloud for processing as well as reasoning. Such disparate networks raise...

-
Combinatorial Cryptography and Latin Squares
In this chapter, we first overview the applications of combinatorics in cryptography. Then, we take look at some historical applications of...
-
The Many Approaches to Innovation Strategy
Innovation strategy is a core part of corporate strategy. This chapter has the objective of defining a rigorous link between the main approaches and...
