Search
Search Results
-
Full threshold change range of threshold changeable secret sharing
A threshold changeable secret sharing (TCSS) scheme is designed for changing the initial threshold pair of the privacy threshold and reconstruction...

-
Changeable essential threshold secret image sharing scheme with verifiability using bloom filter
In threshold secret image sharing schemes (k, n), the secret image S is distributed among n shareholders. To recover the secret image, at least k...

-
A (t, n) threshold quantum image secret sharing scheme
In this paper, a ( t , n ) threshold quantum image secret sharing scheme based on combination theory is proposed. Here, the threshold t is a constant...

-
Boolean operation based lossless threshold secret image sharing
Secret image sharing is a security technique which plays its role in multi-user environment. Secret image sharing using binary operation is a fast...

-
(k, n) threshold secret image sharing scheme based on Chinese remainder theorem with authenticability
In the traditional secret image sharing (SIS) scheme, the secret image is divided into several noise-like shares, which lack authentication and may...

-
A novel threshold changeable secret sharing scheme
A ( t, n ) threshold secret sharing scheme is a fundamental tool in many security applications such as cloud computing and multiparty computing. In...
-
On modular (CRT-based) secret sharing
Secret sharing scheme (SSS) allows to share some secret s among n parties in such a way that only certain subsets of them can recover the secret. The...

-
A Lattice-Based Single-Share Secret Sharing Scheme
In general, in a secret sharing scheme, the dealer chooses shares and distributes them to the participants securely. For the secure communication,...

-
Unconditionally secure non-malleable secret sharing and circular external difference families
Various notions of non-malleable secret sharing schemes have been considered. In this paper, we review the existing work on non-malleable secret...
-
ROMSS: a rational optional multi-secret sharing scheme based on reputation mechanism
The traditional threshold secret sharing scheme only allows the participants’ sub-secret shares to be used once in the reconstruction process....

-
Multi-party codebook distribution strategy based on secret sharing
The paper addresses the issue of secure distribution of codebooks in the field of information security, particularly in the domain of covert...

-
FPGA acceleration of secret sharing for 3D data cubes
Secret sharing can protect the security of important secret information in the network environment. However, the computational complexity and...

-
A framework for counting based secret sharing scheme for images
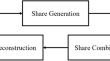
The existing secret sharing schemes used to protect sensitive multimedia data in distributed forms often compromise either security or computational...

-
Preserving friendly stacking and weighted shadows in selective scalable secret image sharing
With advancement of technology, the technique of selective scalable secret image sharing (SSSIS) was first proposed in 2017 as a new alternative of...

-
A GPU scheme for multi-secret visual sharing with varied secret dimensions and contrast enhancement using blind super-resolution
Multi-secret visual sharing schemes are essential for secure and efficient sharing of sensitive visual information. However, existing schemes often...

-
Progressive secret image sharing based on Boolean operations and polynomial interpolations
With the expansion of network bandwidth and the rise of social networks, image sharing on open networks has become a trend. The ensuing privacy...

-
A survey on counting-based secret sharing schemes for resource-constrained environments: techniques, security, challenges, and future directions
Secret sharing schemes play a vital role in securely distributing a secret among multiple participants, ensuring confidentiality and access control....

-
Cheating identifiable polynomial based secret sharing scheme for audio and image
Polynomial based secret sharing is the art of protecting information and a tool used in areas where a secret has to be distributed among multiple...

-
Novel key-integration to safeguard counting-based secret-sharing from possibilities of cyberattack breaches
In the face of malicious cyberattacks, classic security approaches like cryptography and steganography are becoming not sufficient. Secrecy are...
-
Compressed sensing based visually secure multi-secret image encryption-sharing scheme
The existing encryption schemes of visually secure image have drawbacks, such as excessive concentration of image data and insufficient resistance to...

