Search
Search Results
-

-
Generating Signed Permutations by Twisting Two-Sided Ribbons
We provide a simple approach to generating all \(2^n \cdot n!\)...
-
Sequences, Series, and Permutations and Combinations
This chapter discusses sequences, series, and permutations and combinations. Arithmetic and geometric sequences and series are discussed and we...
-
Recursive inversion models for permutations
We develop a new exponential family model for permutations that can capture hierarchical structure in preferences, and that has the well known...

-
The sequence reconstruction problem for permutations with the Hamming distance
V. Levenshtein first proposed the sequence reconstruction problem in 2001. This problem studies the same sequence from some set is transmitted over...
-
On a conjecture on APN permutations
The single trivariate representation proposed in [C. Beierle, C. Carlet, G. Leander, L. Perrin, A Further Study of Quadratic APN Permutations in...
-
On decompositions of permutation polynomials into quadratic and cubic power permutations
Decomposing permutation polynomials into power permutations of small algebraic facilitates the reduction of hardware area requirements when symmetric...
-
Revisiting the Indifferentiability of the Sum of Permutations
The sum of two n-bit pseudorandom permutations is known to behave like a pseudorandom function with n bits of security. A recent line of research has...
-
Reconstruction of permutations distorted by single Kendall τ-errors
Levenshtein first put forward the sequence reconstruction problem in 2001. This problem sets a model in which a sequence from some set is transmitted...
-
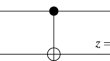
Keyed Sum of Permutations: A Simpler RP-Based PRF
Idealized constructions in cryptography prove the security of a primitive based on the security of another primitive. The challenge of building a...
-
Decoding Tree Decompositions from Permutations
Most algorithmic strategies for solving problems considering treewidth parameterization require that a tree decomposition is given. Given a graph...
-
A note on “Cryptographically strong permutations from the butterfly structure”
Very recently, a class of cryptographically strong permutations with boomerang uniformity 4 and the best known nonlinearity is constructed from the...
-
Security Proofs for Key-Alternating Ciphers with Non-Independent Round Permutations
This work studies the key-alternating ciphers (KACs) whose round permutations are not necessarily independent. We revisit existing security proofs...
-
Correlations Between (Nonlinear) Combiners of Input and Output of Random Functions and Permutations
Linear cryptanalysis considers correlations between linear input and output combiners for block ciphers and stream ciphers. Daemen and Rijmen (2007)...
-
A Difference-Equation-Based Robust Image Encryption Scheme with Chaotic Permutations and Logic Gates
Image encryption has become an indispensable tool for achieving highly secure image-based communications. Numerous encryption approaches have...
-
Multi-user BBB security of public permutations based MAC
At CRYPTO 2019, Chen et al. have shown a beyond the birthday bound secure n -bit to n -bit PRF based on public random permutations. Followed by the...

-
Minwise-Independent Permutations with Insertion and Deletion of Features
The seminal work of Broder et al. [5] introduces the \(\textrm{minHash}\)...
-
New Algorithm for Exhausting Optimal Permutations for Generalized Feistel Networks
The Feistel construction is one of the most studied ways of building block ciphers. Several generalizations were proposed in the literature, leading...
