Search
Search Results
-
Generalized partially bent functions, generalized perfect arrays, and cocyclic Butson matrices
In a recent survey, Schmidt compiled equivalences between generalized bent functions, group invariant Butson Hadamard matrices, and abelian splitting...
-
Families of multi-level Legendre-like arrays
Families of new, multi-level integer 2 D arrays are introduced here as an extension of the well-known binary Legendre sequences that are derived from...
-
Low-complexity arrays of patch signature for efficient ancient coin retrieval
We present a new recognition framework for ancient coins struck from the same die. It is called Low-complexity Arrays of Patch Signatures. To...

-
Generalized nonconvex regularization for tensor RPCA and its applications in visual inpainting
AbstractAs a demonstrated and foremost approach of extracting the key features from corrupted observations, tensor robust principal component...

-
eGHWT: The Extended Generalized Haar–Walsh Transform
Extending computational harmonic analysis tools from the classical setting of regular lattices to the more general setting of graphs and networks is...

-
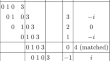
Generalized binary arrays from quasi-orthogonal cocycles
Generalized perfect binary arrays (GPBAs) were used by Jedwab to construct perfect binary arrays. A non-trivial GPBA can exist only if its energy is...
-

-
Quantum image encryption algorithm based on generalized Arnold transform and Logistic map
In the era of big data, image security and real-time processing become more and more important and increasingly difficult to satisfy. To improve the...

-
On security properties of all-or-nothing transforms
All-or-nothing transforms have been defined as bijective map**s on all s -tuples over a specified finite alphabet. These map**s are required to...

-
Large sets with multiplicity
Large sets of combinatorial designs has always been a fascinating topic in design theory. These designs form a partition of the whole space into...
-
MinJoin++: a fast algorithm for string similarity joins under edit distance
We study the problem of computing similarity joins under edit distance on a set of strings. Edit similarity joins is a fundamental problem in...

-
Working Memory for Online Memory Binding Tasks: A Hybrid Model
Working memory is the brain module that holds and manipulates information online. In this work, we design a hybrid model in which a simple...

-
Combinatorial Properties of Fibonacci Arrays
The non-trivial extension of Fibonacci words to Fibonacci arrays was proposed by Apostolico and Brimkov in order to study repetitions in arrays. In...
-
Efficient FPGA implementation for sound source separation using direction-informed multichannel non-negative matrix factorization
Sound source separation (SSS) is a fundamental problem in audio signal processing, aiming to recover individual audio sources from a given mixture. A...

-
Image thresholding method based on Tsallis entropy correlation
Image segmentation is an initial task in many vision-based systems and plays an important role in the processes of image analysis, target recognition...

-
Status of three classes of sequences
Pseudorandom sequences, sometimes shortened as sequences, have played a key role in the applications of digital communications, cryptography and...
-
A Learned Prefix Bloom Filter for Spatial Data
Learned bloom filter (LBF) model has been proposed in recent work to replace the traditional bloom filter (BF). It can reduce the needed amount of...
-
Highly accurate memristor modelling using MOS transistor for analog applications
Memristor technology has grown at a breakneck pace over the last decade, with the promise to transform data processing and storage. A memristor is a...

-
Evaluating Defensive Countermeasures for Software-Based Hardware Abstraction
Protecting software from illegal reverse engineering and malicious hackers is often remedied through either legal or technical means. In the...
-
Heuristically Enhanced IPO Algorithms for Covering Array Generation
The construction of covering arrays (CAs) with a small number of rows is a difficult optimization problem. CAs generated by greedy methods are often...
