Search
Search Results
-
Detecting malicious transactions in database using hybrid metaheuristic clustering and frequent sequential pattern mining
Database systems have become imperative for organisations around the world to store and analyse information. However, as one of the ramifications of...

-
Graph-based substructure pattern mining with edge-weight
To represent complex inter-relationships among entities, weighted graphs are more useful than their unweighted counterparts. In a transactional graph...

-
Exploring image data association: A hybrid mining approach
In this paper, a new approach for mining image association rules is presented, which involves the fine-tuned CNN model, as well as the proposed FIAR...

-
Literature review on Intention Mining-oriented Process Mining in information system
Process Mining focused only on the activity-oriented process and neglected the users’ behaviors behind the activities, which led to overlooking the...

-
A residual utility-based concept for high-utility itemset mining
Knowledge discovery in databases aims at finding useful information for decision-making. The problem of high-utility itemset mining (HUIM) has...
-
3P-ECLAT: mining partial periodic patterns in columnar temporal databases
Partial periodic pattern (3P) mining is a vital data mining technique that aims to discover all interesting patterns that have exhibited partial...

-
New approaches for mining high utility itemsets with multiple utility thresholds
Recently, two research directions have been noticed in data mining: frequent itemset mining (FIM) and high utility itemset mining (HUIM). The FIM...

-
MFS-SubSC: an efficient algorithm for mining frequent sequences with sub-sequence constraint
Mining frequent sequences (FS) with constraints in a sequence database (SDB) are a critical task in Data Mining, as it forms the basis for...

-
Fast privacy-preserving utility mining algorithm based on utility-list dictionary
Privacy preserving utility mining (PPUM) aims to solve the problem of sensitive information leakage in utility pattern mining. In recent years,...

-
A new algorithm using integer programming relaxation for privacy-preserving in utility mining
High-utility itemset mining (HUIM) is an effective technique for discovering significant information in data. However, data containing sensitive and...

-
CCSMP: an efficient closed contiguous sequential pattern mining algorithm with a pattern relation graph
The closed contiguous sequential pattern combines the advantages of closedness constraints and contiguity constraints and in recent years has been...

-
MMC: efficient and effective closed high-utility itemset mining
Analyzing many high-utility itemsets using HUIM methods is challenging and time-consuming. To solve this issue, Closed High-Utility Itemsets (CHUI),...

-
An Experimental Evaluation of Summarisation-Based Frequent Subgraph Mining for Subgraph Searching
The subgraph searching is a fundamental operation for the analysis and exploration of graphs. Nowadays, molecular databases are nearing close to one...

-
Bibliometric mining of research directions and trends for big data
In this paper a program and methodology for bibliometric mining of research trends and directions is presented. The method is applied to the research...

-
Mining for Enthalpy-Based Average High-Utility Patterns with Tighter Upper Bounds
Mining for high average-utility item sets in a quantitative database is develo** the traditional problem of frequent item data mining, with several...

-
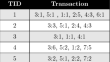
Extracting sequential frequent itemsets from probabilistic sequences database
Computers now handle large amounts of data, leading to the emergence of data mining as a science to extract useful information from this data....

-
Post–mining on Association Rule Bases
Association rule mining identifies potentially unknown correlations between columns in a relational database and is therefore a central task in the...
-
High utility itemsets mining from transactional databases: a survey
AbstractMining high utility itemsets are the basic task in the area of frequent itemset mining (FIM) that has various applications in diverse...

-
Text Mining
These days a large portion of the data exists in the form of text. This motivates us to have the methods for processing this data so that meaningful...
-
Privacy-preserving data (stream) mining techniques and their impact on data mining accuracy: a systematic literature review
This study investigates existing input privacy-preserving data mining (PPDM) methods and privacy-preserving data stream mining methods (PPDSM),...

