Search
Search Results
-
Safety-Aware Apprenticeship Learning
Apprenticeship learning (AL) is a kind of Learning from Demonstration techniques where the reward function of a Markov Decision Process (MDP) is...
-
The “Grey Area”: A Computational Approach to Model the Zone of Proximal Development
In this paper, we propose a computational approach to model the Zone of Proximal Development (ZPD) using predicted probabilities of correctness while...
-
Post-optimization Issues
On page 136 we’ll present a detailed examination of training bias, and on page 323 we’ll see a powerful way to deal with this serious problem. But...
-
Rethinking Causality in Biological and Neural Mechanisms: Constraints and Control
Existing accounts of mechanistic causation are not suited for understanding causation in biological and neural mechanisms because they do not have...

-
Big Data and FinTech
In this chapter, we examine the research issues related to the real-time and mobile data analytics in the area of FinTechs. The issues examined...
-
Predicting Foreground Object Ambiguity and Efficiently Crowdsourcing the Segmentation(s)
We propose the ambiguity problem for the foreground object segmentation task and motivate the importance of estimating and accounting for this...

-
Recurrent Neural Networks
“Democracy is the recurrent suspicion that more than half the people are right more than half the time.”—The New Yorker, July 3, 1944.
-
Introduction to DevOps
New ways of working or new methodologies begin to unearth because of a problem---yes, it all starts with a problem. DevOps too had its own reasons....
-
Evolutionary Approach to Gene Regulatory Networks
Gene regulatory networks (GRNs) described in this chapter are recently attracting attention as a model that can learn in a way similar to neural...
-
A Meta-Review of Feature Selection Techniques in the Context of Microarray Data
Microarray technologies produce very large amounts of data that need to be classified for interpretation. Large data coupled with small sample sizes...
-
The blending interpolation algorithm based on image features
In this paper, we develop a blending interpolation model with help of classical bivariate rational interpolation. The blending model is an organic...

-
Are tweets useful in the bug fixing process? An empirical study on Firefox and Chrome
When encountering an issue, technical users (e.g., developers) usually file the issue report to the issue tracking systems. But non-technical...

-
Dijkstra, Hoare and Parnas
This Chapter focuses on the approach of Dijkstra, Hoare and Parnas. We discuss the calculus of weakest preconditions developed by Dijkstra and the...
-
Improving design decomposition (extended version)
Decomposing a system into subsystems is essential to the design of large software systems. Traditionally, it is performed intuitively without...
-
Deep Reinforcement Learning
“The reward of suffering is experience.”—Harry S. Truman
-
A study of the relation of mobile device attributes with the user-perceived quality of Android apps
The number of mobile applications (apps) and mobile devices has increased considerably over the past few years. Online app markets, such as the...

-
Fault trees on a diet: automated reduction by graph rewriting
Fault trees are a popular industrial technique for reliability modelling and analysis. Their extension with common reliability patterns, such as...
-
Static and Self-Adjusting Mutation Strengths for Multi-valued Decision Variables
The most common representation in evolutionary computation are bit strings. With very little theoretical work existing on how to use evolutionary...

-
Survivability
Survival is the most instinctual behavior of all animals. It is also the most essential design strategy used in robotic and network systems, which...
-
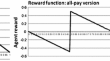
Efficient bidding strategies for Cliff-Edge problems
In this paper, we propose an efficient agent for competing in Cliff-Edge (CE) and simultaneous Cliff-Edge (SCE) situations. In CE interactions, which...