Search
Search Results
-
Explicit constructions of NMDS self-dual codes
Near maximum distance separable (NMDS) codes are important in finite geometry and coding theory. Self-dual codes are closely related to...
-
Evaluative Item-Contrastive Explanations in Rankings
The remarkable success of Artificial Intelligence in advancing automated decision-making is evident both in academia and industry. Within the...

-
A deep learning based cognitive model to probe the relation between psychophysics and electrophysiology of flicker stimulus
The flicker stimulus is a visual stimulus of intermittent illumination. A flicker stimulus can appear flickering or steady to a human subject,...

-
Improving Likert scale big data analysis in psychometric health economics: reliability of the new compositional data approach
Bipolar psychometric scales data are widely used in psychologic healthcare. Adequate psychological profiling benefits patients and saves time and...

-

-
Multidimensional graph transformer networks for trajectory prediction in urban road intersections
With the rapid development of autonomous driving, accurately predicting the future movement trajectories of various agents in complex scenarios, such...

-
Granular Syntax Processing with Multi-Task and Curriculum Learning
Syntactic processing techniques are the foundation of natural language processing (NLP), supporting many downstream NLP tasks. In this paper, we...

-
Twin Bounded Support Vector Machine with Capped Pinball Loss
In order to obtain a more robust and sparse classifier, in this paper, we propose a novel classifier termed as twin bounded support vector machine...

-
Prescribed-Time Sampled-Data Control for the Bipartite Consensus of Linear Multi-Agent Systems in Singed Networks
This article examines the prescribed-time sampled-data control problem for multi-agent systems in signed networks. A time-varying high gain-based...

-
Vectorial negabent concepts: similarities, differences, and generalizations
In Pasalic et al. (IEEE Trans Inf Theory 69:2702–2712, 2023), and in Anbar and Meidl (Cryptogr Commun 10:235–249, 2018), two different vectorial...
-
Pruning Deep Neural Networks for Green Energy-Efficient Models: A Survey
Over the past few years, larger and deeper neural network models, particularly convolutional neural networks (CNNs), have consistently advanced...

-
Some self-dual codes and isodual codes constructed by matrix product codes
In 2020, Cao et al. proved that any repeated-root constacyclic code is monomially equivalent to a matrix product code of simple-root constacyclic...
-
Some constacyclic BCH codes with good parameters
BCH codes as a subclass of constacyclic BCH codes have been widely studied, while the results on the parameters of BCH codes over finite fields are...
-
Unmasking GAN-Generated Faces with Optimal Deep Learning and Cognitive Computing-Based Cutting-Edge Detection System
The emergence of deep learning (DL) has improved the excellence of generated media. However, with the enlarged level of photorealism, synthetic media...

-
A survey of multi-population optimization algorithms for tracking the moving optimum in dynamic environments
The solution spaces of many real-world optimization problems change over time. Such problems are called dynamic optimization problems (DOPs), which...

-
Cognitive Intelligent Decisions for Big Data and Cloud Computing in Industrial Applications using Trifold Algorithms
In contemporary real-time applications, diminutive devices are increasingly employing a greater portion of the spectrum to transmit data despite the...

-
Security analysis of the ISO standard \(\textsf{OFB}\)-\(\textsf{DRBG}\)
Deterministic random bit generators (DRBGs) are essential tools in modern cryptography for generating secure and unpredictable random numbers. The...

-
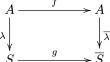
A survey of compositional inverses of permutation polynomials over finite fields
In this paper, we survey on the recent results and methods in the study of compositional inverses of permutation polynomials over finite fields. In...