Abstract
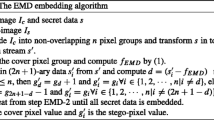
Steganography provides secure communications over the Internet with a cover image. However, it is difficult to transfer many messages with small-sized images. We have improved EMD (Exploiting Modification Direction), proposed by Zhang and Wang, to solve this problem. In this paper, we have developed a (2n + 2-1)-ary scheme. Our scheme shows a higher embedding rate, R=log2(2n + 2-1)/n, which is greater than that of the EMD scheme, because the EMD scheme embedding rate is R=log2(2n+1)/n, for n>=2. The experimental results show that our scheme is able to embed twice as many secret bits in multimedia communications compared to the existing EMD embedding method. Our method has low complexity and achieves higher embedding performance with good perceptual quality against the earlier arts. An experiment verified our proposed data hiding method in multimedia communications.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Wang, H., Wang, S.: Cyber warfare:steganography vs. steganalysis. Communication of the ACM 47(10), 76–82 (2004)
Goljan, M., Hogea, D., Soukal, D.: Quantitative Steganalysis of Digital Images: Estimating the Secret Message Length. ACM Multimedia Systems Journal, Special Issue on Multimedia Security 9(3), 288–302 (2003)
Katzenbeisser, S., Petitcolas, F.A.P. (eds.): Information Hiding Techniques for Steganography and Digital Watermarking. Artech House Books, Boston (2000) ISBN I-58053-35-4
Westfeld, A.: F5-A steganographic algorithm. In: Moskowitz, I.S. (ed.) IH 2001. LNCS, vol. 2137, pp. 289–302. Springer, Heidelberg (2001)
Provos, N., Honeyman, P.: Hide and Seek: An Introduction to Steganography. IEEE Security and Privacy 1(3), 32–44 (2003)
Yua, Y.-H., Changa, C.-C., Hub, Y.-C.: Hiding secret data in images via predictive coding. Pattern Recognition 38(5), 691–705 (2005)
Mielikainen, J.: LSB matching revisited. IEEE Signal Processing Letters 13(5), 285–287 (2006)
Chan, C.-K., Cheng, L.M.: Hiding data in images by simple LSB substitution. Pattern Recognition 37(3), 469–474 (2004)
Lin, I.-C., Lin, Y.-B., Wang, C.-M.: Hiding data in spatial domain images with distortion tolerance. Computer Standards and Interfaces 31(2), 458–464 (2009)
Chang, C.C., Chen, T.S., Chung, L.Z.: A steganographic method based upon JPEG and quantization table modification. Information Sciences-Informatics and Computer Science 141(1-2), 123–138 (2002)
Spauldinga, J., Noda, H., Shirazib, M.N., Kawaguchia, E.: BPCS steganography using EZW lossy compressed images. Pattern Recognition Letters 23(13), 1579–1587 (2002)
Zhang, X., Wang, S.: Efficient Steganographic Embedding by Exploiting Modification Direction. IEEE Communications Letters 10(11), 781–783 (2006)
Lee, C.-F., Chang, C.-C., Wang, K.-H.: An improvement of EMD embedding method for large payloads by pixel segmentation strategy. Image and Vision Computing 26(12), 1670–1676 (2008)
Fridrich, J., Goljan, M., Du, R.: Detecting LSB steganography in color, and gray-scale images. IEEE Trans. Multimedia 8, 22–28 (2001)
Westfe3d, A., Pfitzmann, A.: Attacks on Steganographic Syste. In: Proc. 3rd Information Hiding Workshops, Dresden, Germany, September 28-October 1, pp. 61–75 (1999)
Goljan, M., Soukal, D.: Higher-Order Statistical Steganalysis of Palette Images. In: Proc. SPIE, Electronic Imaging, Security, Steganography, Watermarking of Multimedia Contents V, Santa Clara, California, pp. 178–190 (2003)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2011 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Kim, C., Shin, D., Shin, D., Zhang, X. (2011). Improved Steganographic Embedding Exploiting Modification Direction in Multimedia Communications. In: Park, J.J., Lopez, J., Yeo, SS., Shon, T., Taniar, D. (eds) Secure and Trust Computing, Data Management and Applications. STA 2011. Communications in Computer and Information Science, vol 186. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-22339-6_16
Download citation
DOI: https://doi.org/10.1007/978-3-642-22339-6_16
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-22338-9
Online ISBN: 978-3-642-22339-6
eBook Packages: Computer ScienceComputer Science (R0)