Abstract
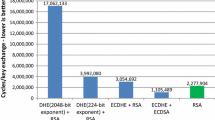
This paper is the first to investigate the power of the Cell Broadband Engine for state-of-the-art public-key cryptography. We present a high-speed implementation of elliptic-curve Diffie-Hellman (ECDH) key exchange for this processor, which needs 697080 cycles on one Synergistic Processor Unit for a scalar multiplication on a 255-bit elliptic curve, including the costs for key verification and key compression. This cycle count is independent of inputs therefore protecting against timing attacks.
This speed relies on a new representation of elements of the underlying finite field suited for the unconventional instruction set of this architecture.
Furthermore we demonstrate that an implementation based on the multi-precision integer arithmetic functions provided by IBM’s multi-precision math (MPM) library would take at least 2227040 cycles. Comparison with implementations of the same function for other architectures shows that the Cell Broadband Engine is competitive in terms of cost-performance ratio to other recent processors such as the Intel Core 2 for public-key cryptography.
Specifically, the state-of-the-art Galbraith-Lin-Scott ECDH software performs 27370 scalar multiplications per second using all four cores of a 2.5GHz Intel Core 2 Quad Q9300 inside a $296 computer, while the new software reported in this paper performs 27474 scalar multiplications per second on a Playstation 3 that costs just $221. Both of these speed reports are for high-security 256-bit elliptic-curve cryptography.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Alvaro, W., Kurzak, J., Dongarra, J.: Fast and small short vector SIMD matrix multiplication kernels for the synergistic processing element of the CELL processor. In: Bubak, M., van Albada, G.D., Dongarra, J., Sloot, P.M.A. (eds.) ICCS 2008, Part I. LNCS, vol. 5101, pp. 935–944. Springer, Heidelberg (2008)
Bernstein, D.J.: qhasm: tools to help write high-speed software, http://cr.yp.to/qhasm.html (accessed January 1, 2009)
Bernstein, D.J.: Curve25519: new Diffie-Hellman speed records. In: Yung, M., Dodis, Y., Kiayias, A., Malkin, T.G. (eds.) PKC 2006. LNCS, vol. 3958, pp. 207–228. Springer, Heidelberg (2006)
Bernstein, D.J., Lange, T. (eds.): eBACS: ECRYPT benchmarking of cryptographic systems (November 2008), http://bench.cr.yp.to/ (accessed January 1, 2009)
Costigan, N., Scott, M.: Accelerating SSL using the vector processors in IBM’s Cell Broadband Engine for Sony’s Playstation 3. In: Proceedings of SPEED workshop (2007), http://www.hyperelliptic.org/SPEED/
Diffie, W., Hellman, M.E.: New directions in cryptography. IEEE Transactions on Information Theory IT-22(6), 644–654 (1976), http://citeseer.ist.psu.edu/diffie76new.html
Fan, J., Sakiyama, K., Verbauwhede, I.: Elliptic curve cryptography on embedded multicore systems. In: Workshop on Embedded Systems Security - WESS 2007, Salzburg, Austria, pp. 17–22 (2007)
Galbraith, S.D., Lin, X., Scott, M.: Endomorphisms for faster elliptic curve cryptography on general curves (2008), http://eprint.iacr.org/2008/194
Gaudry, P., Thomé, E.: The mp\(\mathbb{F}_q\) library and implementing curve-based key exchanges. In: Proceedings of SPEED workshop (2007), http://www.loria.fr/~gaudry/publis/mpfq.pdf
Grabher, P., Großchädl, J., Page, D.: On software parallel implementation of cryptographic pairings. In: Selected Areas in Cryptography – SAC 2008. LNCS, vol. 5381, pp. 34–49. Springer, Heidelberg (to appear)
Hankerson, D., Menezes, A.J., Vanstone, S.A.: Guide to Elliptic Curve Cryptography. Springer, Berlin (2003)
IBM DeveloperWorks. Cell broadband engine architecture and its first implementation (November 2005), http://www-128.ibm.com/developerworks/power/library/pa-cellperf/
IBM DeveloperWorks. Cell broadband engine programming handbook (version 1.1) (April 2007), http://www-01.ibm.com/chips/techlib/techlib.nsf/techdocs/9F820A5FFA3ECE8C8725716A0062585F
IBM DeveloperWorks. SPU assembly language specification (version 1.6) (September 2007), http://www-01.ibm.com/chips/techlib/techlib.nsf/techdocs/EFA2B196893B550787257060006FC9FB
IBM DeveloperWorks. Example library API reference (version 3.1) (September 2008), http://www.ibm.com/developerworks/power/cell/documents.html .
IBM DeveloperWorks. SPE cryptographic library user documentation 1.0 (September 2008), http://www.ibm.com/developerworks/power/cell/documents.html .
Montgomery, P.L.: Speeding the Pollard and elliptic curve methods of factorization. Mathematics of Computation 48(177), 243–264 (1987)
Shimizu, K., Brokenshire, D., Peyravian, M.: Cell Broadband Engine support for privacy, security, and digital rights management applications. White paper, IBM (October 2005), http://www-01.ibm.com/chips/techlib/techlib.nsf/techdocs/3F88DA69A1C0AC40872570AB00570985
Sotirov, A., Stevens, M., Appelbaum, J., Lenstra, A., Molnar, D., Osvik, D.A., de Weger, B.: MD5 considered harmful today (December 2008), http://www.win.tue.nl/hashclash/rogue-ca/ (accessed January 4, 2009)
Stevens, M., Lenstra, A., de Weger, B.: Nostradamus – predicting the winner of the 2008 US presidential elections using a Sony PlayStation 3 (November 2007), http://www.win.tue.nl/hashclash/Nostradamus/ (accessed January 4, 2009)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2009 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Costigan, N., Schwabe, P. (2009). Fast Elliptic-Curve Cryptography on the Cell Broadband Engine. In: Preneel, B. (eds) Progress in Cryptology – AFRICACRYPT 2009. AFRICACRYPT 2009. Lecture Notes in Computer Science, vol 5580. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-02384-2_23
Download citation
DOI: https://doi.org/10.1007/978-3-642-02384-2_23
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-02383-5
Online ISBN: 978-3-642-02384-2
eBook Packages: Computer ScienceComputer Science (R0)