Abstract
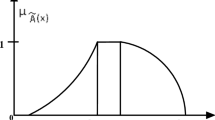
This work uses the fuzzy weight strategy to construct a novel image interpolation method. By taking into account the fuzzy weight value of each pair of pixels in a chosen block, the interpolated pixel values are created. Each input pixel pair’s fuzzy membership values have been taken to represent the range between the block’s minimum and maximum value. The input membership value is fed into the fuzzy output function, which calculates the fuzzy rule’s strength using the Max–Min composite principle. Then, through a defuzzification process, interpolated pixel values are calculated from the fuzzy output function dependent on the strength of the fuzzy rule. In actuality, fuzzy weight based interpolation algorithms create virtual pixels, which are superior to the interpolation techniques now in use. The results of the experiments show that the suggested method almost always produced images with the highest PSNR. So, in the suggested technique, the FWS was used to generate the improved cover image.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Fridrich J (2009) Steganography in digital media: principles, algorithms, and applications. Cambridge Univ. Press, Cambridge, UK
Panah AS, Van Schyndel R, Sellis T, Bertino E (2016) On the properties of non-media digital watermarking: a review of state of the art techniques. IEEE Access 4:2670–2704. https://doi.org/10.1109/ACCESS.2016.2570812
Singh S, Singh AK, Ghrera SP (2017) A recent survey on data hiding techniques. In: 2017 international conference on I-SMAC (IoT in Social, Mobile, Analytics and Cloud) (I-SMAC). IEEE, pp 88–886
Chowdhury FS, Dhar PK, Deb K, Koshiba T (2020) Blind image watermarking in canonical and cepstrum domains based on 4-connected t-o’clock scrambling. Symmetry 12(2):266
Jana B, Giri D, Mondal SK (2017) Partial reversible data hiding scheme using (7, 4) hamming code. Multimedia Tools Appl 76(20):21691–21706
Jana B (2016) High payload reversible data hiding scheme using weighted matrix. Optik 127(6):3347–3358
Jana M, Jana B (2020) An improved data hiding scheme through image interpolation. In: Computational intelligence in pattern recognition. Springer, pp 157–169
Gunjan R, Pandia P, Mohnot R (2017) Secure extraction of image data based on optimized transform method. In: 2017 IEEE 4th international conference on cyber security and cloud computing (CSCloud). IEEE, pp 217–222
Gonge SS, Ghatol AA (2017) An enhancement in security and copyright protection technique used for digital still image. In: 2017 international conference on nascent technologies in engineering (ICNTE). IEEE, pp 1–9
Pushpad A, Potnis AA (2017) Improved image security scheme using combination of image encryption and reversible watermarking. In: 2017 4th international conference on signal processing and integrated networks (SPIN). IEEE, pp 293–297
Rasti P, Anbarjafari G, Demirel H (2017) Colour image watermarking based on wavelet and qr decomposition. In: 2017 25th signal processing and communications applications conference (SIU). IEEE, pp 1–4
Kelkar V, Mehta JH, Tuckley K (2018) A novel robust reversible watermarking technique based on prediction error expansion for medical images. In: Proceedings of 2nd international conference on computer vision and image processing. Advances in intelligent systems and computing, vol 703, pp 131–143
Shehab A, Elhoseny M, Muhammad K, Sangaiah AK, Yang P, Huang H, Hou G (2018) Secure and robust fragile watermarking scheme for medical images. IEEE Access 6:10269–10278
Liu J, Li J, Ma J, Sadiq UN, Yang A (2019) A robust multi-watermarking algorithm for medical images based on DTCWT-DCT and Henon map. Appl Sci 9(4):1–23
Rehman A, Sultan K, Aldhafferi N, Alqahtiani A, Mahmood M (2018) Reversible and fragile watermarking scheme for medical images. Comput Math Methods Med 18:7
Zhang H, Wang C, Zhou X (2017) Fragile watermarking for image authentication using the characteristic of SVD. Algorithms 10(1):1–12
Konstantinides K, Natarajan B, Yovanof GS (1997) Noise estimation and filtering using block-based singular value decomposition. IEEE Trans Image Process 6(3):479–483
Liu R, Tan T (1997) An SVD-based watermarking scheme for protecting rightful ownership. IEEE Trans Image Process 6(3):479–483
Roy S, Pal AK (2017) An indirect watermark hiding in discrete cosine transform singular value decomposition domain for copyright protection. Roy Soc Open Sci 4(6). Art. no. 170326
Makbol NM, Khoo BE, Rassem TH (2016) Block-based discrete wavelet transform-singular value decomposition image watermarking scheme using human visual system characteristics. IET Image Process 10(1):34–52
Wenyin Z, Shih FY (2011) Semi-fragile spatial watermarking based on local binary pattern operators. Opt Commun 284(16–17):3904–3912
Ojala T, Pietikainen M, Maenpaa T (2002) Multiresolution gray-scale and rotation invariant texture classification with local binary patterns. IEEE Trans Pattern Anal Mach Intell 24(7):971–987
Fan L, Gao T, Cao Y (2013) Improving the embedding efficiency of weight matrix-based steganography for grayscale images. Comput Electr Eng 39(3):873–881
Tseng YC, Chen YY, Pan HK (2002) A secure data hiding scheme for binary images. IEEE Trans Commun 50(8):1227–1231
Jana B (2016) High payload reversible data hiding scheme using weighted matrix. Optik-Int J Light Electron Opt 127(6):3347–3358
Chowdhuri P, Pal P, Jana B (2019) Improved data hiding capacity through repeated embedding using modified weighted matrix for color image. Int J Comput Appl 41(3):218–232
Kumar S, Dutta A (2016, April) A novel spatial domain technique for digital image watermarking using block entropy. In: 2016 international conference on recent trends in information technology (ICRTIT). IEEE, pp 1–4
Cao Z, Yin Z, Hu H, Gao X, Wang L (2016) High capacity data hiding scheme based on (7, 4) Hamming code. Springer Plus 5(1):1–13
Bai J, Chang CC (2016) A high payload steganographic scheme for compressed images with hamming code. Int J Netw Sec 18(6):1122–1129
Jana B, Giri D, Mondal SK (2018) Dual image based reversible data hiding scheme using (7, 4) hamming code. Multimedia Tools Appl 77(1):763–785
Su Q, Chen B (2018) Robust color image watermarking technique in the spatial domain. Soft Comput 22(1):91–106
Laouamer L (2019, March) A new image watermarking technique in spatial domain using DC coefficients and graph representation. In: International conference on advanced machine learning technologies and applications. Springer, Cham, pp 633–644
Peng F, Zhao Y, Zhang X, Long M, Pan WQ (2020) Reversible data hiding based on RSBEMD coding and adaptive multi-segment left and right histogram shifting. Sig Process Image Commun 81:115715
Hassan FS, Gutub A (2021) Efficient image reversible data hiding technique based on interpolation optimization. Arab J Sci Eng 46(9):8441–8456
Maheswari S, Rameshwaran K, Malarselvi KM (2015) DCT-PCA based watermarking on E-governance documents. Res J Appl Sci Eng Technol 9(7):507–511
Abbas NH, Ahmad SMS, Ramli ARB, Parveen S (2016) A multi-purpose watermarking scheme based on hybrid of lifting wavelet transform and Arnold transform. In: International conference on multidisciplinary in IT and communication science and applications
Ghazvini M, Hachrood EM, Mirzadi M (2017) An improved image watermarking method in frequency domain. J Appl Sec Res 12(2):260–275
Yuan Y, Huang D, Liu D (2006) An integer wavelet based multiple logo-watermarking scheme. In: First international multi-symposiums on computer and computational sciences, Hanzhou, vol 2, pp 175–179
Rangel-Espinoza K, Fragoso-Navarro E, Cruz-Ramos C, Reyes-Reyes R, Nakano-Miyatake M, Perez-Meana HM (2018) Adaptive removable visible watermarking technique using dual watermarking for digital color images. Multimedia Tools Appl 77(11):13047–13074
Jana S, Jana B, Lu T-C, Vo TN (2022) Reversible data hiding scheme exploiting center folding with fuzzy weight strategy
USC-SIPI (2017). University of Southern California. The usc-sipi image database. http://sipi.usc.edu/database/database.php. Accessed 20 Sept 2017
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2024 The Author(s), under exclusive license to Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Haldar, A., Jana, B., Jana, S., Sao, N.K., Vo, T.N. (2024). Secured Information Communication Exploiting Fuzzy Weight Strategy. In: Mandal, J.K., Jana, B., Lu, TC., De, D. (eds) Proceedings of International Conference on Network Security and Blockchain Technology. ICNSBT 2023. Lecture Notes in Networks and Systems, vol 738. Springer, Singapore. https://doi.org/10.1007/978-981-99-4433-0_9
Download citation
DOI: https://doi.org/10.1007/978-981-99-4433-0_9
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-99-4432-3
Online ISBN: 978-981-99-4433-0
eBook Packages: EngineeringEngineering (R0)