Abstract
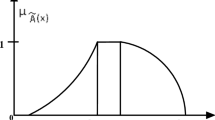
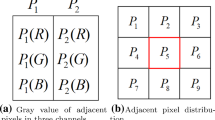
With time, humans have realized, the internet is the best alternative for exchange of messages through multimedia documents, especially images. Thus, its imperceptibility and security are big concerns. Recently, Ashraf et al. (Heliyon 6(5):e03771, [1]) evaluated similarity for image steganography using interval type-2 fuzzy logic, but the visual quality (PSNR) is not as good as current demand. To solve the problem, we have proposed a data hiding scheme by combining distinct and vague characteristics of an image through the techniques of superpixel and fuzzy logic respectively. Superpixel and TSK Fuzzy logic model with rule base is used to identify non-uniform regions of the image where secret bits are embedded in coefficients of quantized Discrete Cosine Transform (DCT). This technique can be used for secret data communications. With an average PSNR of 58 dB, the proposed approach provides excellent visual quality. Finally, in order to illustrate the efficacy of our technique, we compared the proposed system to existing methodologies.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Ashraf Z, Roy ML, Muhuri PK, Lohani QD (2020) Interval type-2 fuzzy logic system based similarity evaluation for image steganography. Heliyon 6(5):e03771
Li B, Wang M, Li X, Tan S, Huang J (2015) A strategy of clustering modification directions in spatial image steganography. IEEE Trans Inf Forensics Secur 10(9):1905–1917
Roy R, Laha S (2015) Optimization of stego image retaining secret information using genetic algorithm with 8-connected PSNR. Procedia Comput Sci 60:468–477
Nipanikar SI, Deepthi VH, Kulkarni N (2018) A sparse representation based image steganography using particle swarm optimization and wavelet transform. Alexandria Eng J 57(4):2343–2356
Sajasi S, Moghadam AME (2013) A high quality image steganography scheme based on fuzzy inference system. In: 2013 13th Iranian conference on fuzzy systems (IFSC). IEEE, pp 1–6
Chao RM, Wu HC, Lee CC, Chu YP (2009) A novel image data hiding scheme with diamond encoding. EURASIP J Inf Secur 2009:1–9
Hussain M, Wahab AWA, Ho AT, Javed N, Jung KH (2017) A data hiding scheme using parity-bit pixel value differencing and improved rightmost digit replacement. Signal Process: Image Commun 50:44–57
Pal P, Chowdhuri P, Jana B (2018) Weighted matrix based reversible watermarking scheme using color image. Multimedia Tools Appl 77(18):23073–23098
Dey A, Pal P, Chowdhuri P, Singh PK, Jana B (2020) Center-Symmetric Local Binary Pattern-Based image authentication using local and global features vector. In: Computational intelligence in pattern recognition. Springer, Singapore, pp 489–501
Pal P, Jana B, Bhaumik J (2021) A secure reversible color image watermarking scheme based on LBP, Lagrange interpolation polynomial and weighted matrix. Multimedia Tools Appl 1-28
Rabie T, Baziyad M, Kamel I (2018) Enhanced high capacity image steganography using discrete wavelet transform and the Laplacian pyramid. Multimedia Tools Appl 77(18):23673–23698
Kadhim IJ, Premaratne P, Vial PJ (2018) Adaptive image steganography based on edge detection over dual-tree complex wavelet transform. In: International conference on intelligent computing. Springer, Cham, pp 544–550
Miaou SG, Hsu CM, Tsai YS, Chao HM (2000) A secure data hiding technique with heterogeneous data-combining capability for electronic patient records. In: Proceedings of the 22nd annual international conference of the IEEE engineering in medicine and biology society (Cat. No. 00CH37143), vol 1. IEEE, pp 280–283
Sridevi T, Fathima SS (2013) Digital image watermarking using fuzzy logic approach based on DWT and SVD. Int J Comput Appl 74(13)
Jamali M, Rafiei S, Soroushmehr SM, Karimi N, Shirani S, Najarian K, Samavi S (2017) Adaptive blind image watermarking using fuzzy inference system based on human visual perception. ar**v:1709.06536
Zadeh LA, Klir GJ, Yuan B (1996) Fuzzy sets, fuzzy logic, and fuzzy systems: selected papers, vol 6. World Scientific
Ren X, Malik J (2003) Learning a classification model for segmentation. In: Null. IEEE, p 10
Tai WL, Yeh CM, Chang CC (2009) Reversible data hiding based on histogram modification of pixel differences. IEEE Trans Circ Syst video Technol 19(6):906–910
Chang CC, Liu Y, Nguyen TS (2014) A novel turtle shell based scheme for data hiding. In: 2014 Tenth international conference on intelligent information hiding and multimedia signal processing. IEEE, pp 89–93
Parah SA, Sheikh JA, Loan NA, Bhat GM (2017) A robust and computationally efficient digital watermarking technique using inter block pixel differencing. In: Multimedia forensics and security. Springer, Cham, pp 223–252
Tai WL, Liao ZJ (2018) Image self-recovery with watermark self-embedding. Signal Process: Image Commun 65:11–25
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2023 The Author(s), under exclusive license to Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Singh, P.K., Jana, B., Datta, K., Mura, P., Chowdhuri, P., Pal, P. (2023). Fuzzy Logic with Superpixel-Based Block Similarity Measures for Secured Data Hiding Scheme. In: Basu, S., Kole, D.K., Maji, A.K., Plewczynski, D., Bhattacharjee, D. (eds) Proceedings of International Conference on Frontiers in Computing and Systems. Lecture Notes in Networks and Systems, vol 404. Springer, Singapore. https://doi.org/10.1007/978-981-19-0105-8_44
Download citation
DOI: https://doi.org/10.1007/978-981-19-0105-8_44
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-19-0104-1
Online ISBN: 978-981-19-0105-8
eBook Packages: EngineeringEngineering (R0)