Abstract
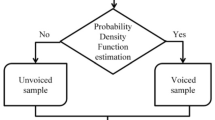
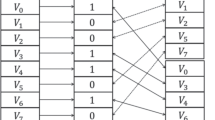
Security is essential to safeguard confidential data. Data in the form of signal, image, text etc. … can be hacked by intruders. Dual-Level Security with Spiral Map** [DLSSM] Scheme is proposed to secure the secret data in unsafe medium. DLSSM encompass cryptography and steganography along with strong spiral map** technique. Cryptographic techniques converts the secret data into cipher data, by which hacker doesn’t understand any information even if they get the data. Spiral map** method enhances the level of security provided to the secret signal. Steganography hides the secret data within another covering file with no traces of the hidden secret data. Hence, dual level security scheme strengthens the system in covert transmission. Speech signals of various Indian languages from IL-LDC and standard corpus are taken as samples to analyse the proposed DLSSM scheme effectiveness. Standard voice signals are considered as input to prove the novelty of the method. The proposed method [DLSSM] is compared with existing systems to prove its efficiency.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Sathiyamurthi, P., Ramakrishnan, S.: Speech encryption using chaotic shift keying for secured speech communication. EURASIP J. Audio Speech Music Process. 2017(1), 1–11 (2017). https://doi.org/10.1186/s13636-017-0118-0
Cohn-Gordon, K., Cremers, C., Dowling, B., Garratt, L., Stebila, D.: A formal security analysis of the signal messaging protocol. In: IEEE European Symposium on Security and Privacy, pp. 451–466 (2017)
Chithra, P.L., Aparna R.: Voice signal encryption scheme using transformation and embedding techniques for enhanced security. In: IEEE Conference on ICISPC 2018, pp. 149–154 (July 2018)
Kohata, M.: Secure speech encryption system using segments for speech synthesis, pp 264–267 (2014)
Farsana, F.J., Gopakumar, K.: A novel approach for speech encryption: Zaslavsky map as pseudo random number generator. In: 6th International Conference on Advances in Computing & Communications, ICACC 2016, pp. 6–8 (September 2016)
Lima, J.B., da Silva Neto, E.F.: Audio encryption based on the cosine number transform. Multimed. Tools Appl. 75(14), 8403–8418 (2015). https://doi.org/10.1007/s11042-015-2755-6
Mostafa, A., Soliman, N.F., Abdalluh, M., Abd El-samie, F.E.: Speech encryption using two dimensional chaotic maps. In: 11th International Conference on Computer Engineering (ICENCO), February 2016. IEEE Xplore (2016)
Aarti, B., Kopparapu, S.: Spoken Indian language identification: a review of features and databases. Sādhanā 43(4), 53:1–53:14 (2018). https://doi.org/10.1007/s12046-018-0841-y. Indian Academy of Sciences
Bhaskararao, P.: Salient phonetic features of Indian languages in speech technology. Sādhanā 36(Part 5), 587–599 (2011). https://doi.org/10.1007/s12046-011-0039-z. Indian Academy of Sciences
Aparna, R., Chithra, P.I.: A review on cryptographic algorithms for speech signal security. Int. J. Emerg. Trends Technol. Comput. Sci. (IJETTCS) 5(5), 84–88 (2016)
Rajanarayanan, S., Pushparaghavan, A.: Recent developments in signal encryption – a critical survey. Int. J. Sci. Res. Publ. 2(6), 1–7 (2012)
Fridrich, J.: Symmetric ciphers based on two-dimensional chaotic maps. Int. J. Bifurcat. Chaos 8(6), 1259–1284 (1998)
Teerakanok, T., Kamolphiwong, S.: Accelerating asymmetric-key cryptography using Parallel-key Cryptographic Algorithm (PCA). In: 2009 6th International Conference on Electrical Engineering/Electronics, Computer, Telecommunications and Information Technology (2009)
Thomas, S.E., et al.: Advanced cryptographic steganography using multimedia files. In: International Conference on Electrical Engineering and Computer Science, ICEECS-2012, pp. 239–242 (2012)
Slimani, D., Merazka, F.: Encryption of speech signal with multiple secret keys. In: International Conference on Natural Language and Speech Processing, ICNLSP 2015, pp. 79–88 (2015)
Saad, N.A., Eman, H.: Speech encryption based on chaotic maps. Int. J. Comput. Appl. 93(4), 19–28 (2014)
Hato, E., Shihab, D.: Lorenz and Rossler chaotic system for speech signal encryption. Int. J. Comput. Appl. 128(11), 09758887 (2015)
Abdul-Majeed, A.M.: Speech encryption using genetic algorithm and Arnold cat map. Int. J. Comput. Sci. Inf. Secur. (IJCSIS) 14(12), 911–915 (2016)
Dutta, S., Das, T., Jash, S., Patra, D., Paul, P.: A cryptography algorithm using the operations of genetic algorithm & pseudo random sequence generating functions. Int. J. Adv. Comput. Sci. Technol. 3(5), 325–330 (2014)
Jhingran, R., Thada, V., Dhaka, S.: A study on cryptography using genetic algorithm. Int. J. Comput. Appl. 118(20), 10–14 (2015)
Chithra, P.L., Aparna, R.: Performance analysis of windowing techniques in automatic speech signal segmentation. Indian J. Sci. Technol. 8(29), 1–7 (2015)
Aparna R., Chithra, P.L.: Role of windowing techniques in speech signal processing for enhanced signal cryptography, chap. 28. In: The Book Advanced Engineering Research and Applications, pp. 446–458 (2017)
Al-Azawi, M.K.M., Gaze, A.M.: Combined speech compression and encryption using chaotic compressive sensing with large key size. IET Sig. Process. 12(2), 214–218 (2018)
Chen, J., Ling, B.W.-K., Feng, P., Lei, R.: Computer cryptography through performing chaotic modulation on intrinsic mode functions with non-dyadic number of encrypted signal. IET Sig. Process. 13(1), 7–13 (2019)
Chen, Y., Hao, J., Chen, J.: End-to-end speech encryption algorithm based on speech scrambling in frequency domain. In: IET Signal Processing, 3rd International Conference on Cyberspace Technology, CCT 2015 (October 2015)
Acknowledgment
We owe our sincere thanks to the Department of Computer Science & Applications, University of Madras & Shri Shankarlal Sundarbai Shasun Jain College for consistent support in carrying the research work.
Author information
Authors and Affiliations
Corresponding authors
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2020 Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Chithra, P.L., Aparna, R. (2020). Dual-Level Security with Spiral Map** [DLSSM] Scheme for Secure Covert Transmission of Speech Signals in Various Indian Languages. In: Badica, C., Liatsis, P., Kharb, L., Chahal, D. (eds) Information, Communication and Computing Technology. ICICCT 2020. Communications in Computer and Information Science, vol 1170. Springer, Singapore. https://doi.org/10.1007/978-981-15-9671-1_6
Download citation
DOI: https://doi.org/10.1007/978-981-15-9671-1_6
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-15-9670-4
Online ISBN: 978-981-15-9671-1
eBook Packages: Computer ScienceComputer Science (R0)