Abstract
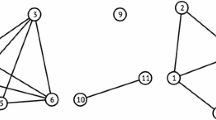
MANETs (mobile ad hoc networks) operate in a self-organised and decentralised way. Attacks against nodes that are highly relied to relay traffic could result in a wide range of service outage. A comprehensive model that could enhance the understanding of network behaviour under attacks is important to the design and construction of resilient self-organising networks. Previously, we modelled MANETs as an aggregation of time-varying graphs into a static weighted graph, in which the weights represent link availability of pairwise nodes. Centrality metrics were used to measure node significance but might not always be optimal. In this paper, we define a new metric called criticality that can capture node significance more accurately than centrality metrics. We demonstrate that attacks based on criticality have greater impact on network performance than centrality-based attacks in real-time MANETs.
Chapter PDF
Similar content being viewed by others
References
The ns-3 network simulator (July 2009), http://www.nsnam.org
Arulselvan, A., Commander, C.W., Elefteriadou, L., Pardalos, P.M.: Detecting critical nodes in sparse graphs. Computers and Operations Research 36(7), 2193–2200 (2009)
Billinton, R., Allan, R.: Reliability Evaluation of Engineering Systems. Plenum Press London (1983)
Borgatti, S.P.: Identifying sets of key players in a social network. Comput. Math. Organ. Theory 12(1), 21–34 (2006)
Camp, T., Boleng, J., Davies, V.: A survey of mobility models for ad hoc network research. Wireless Communications and Mobile Computing 2(5), 483–502 (2002), http://dx.doi.org/10.1002/wcm.72
Çetinkaya, E.K., Broyles, D., Dandekar, A., Srinivasan, S., Sterbenz, J.P.G.: Modelling Communication Network Challenges for Future Internet Resilience, Survivability, and Disruption Tolerance: A Simulation-Based Approach. Springer Telecommunication Systems, 1–16 (2011) (published online: September 21, 2011)
Di Summa, M., Grosso, A., Locatelli, M.: Branch and cut algorithms for detecting critical nodes in undirected graphs. Computational Optimization and Applications, 1–32 (2012)
Dinh, T., Xuan, Y., Thai, M., Park, E., Znati, T.: On approximation of new optimization methods for assessing network vulnerability. In: Proceedings of the IEEE Conference on Computer Communications (INFOCOM), pp. 1–9. IEEE (2010)
Freeman, L.: Centrality in social networks conceptual clarification. Social Networks 1(3), 215–239 (1979)
Kim, T.H., Tipper, D., Krishnamurthy, P., Swindlehurst, A.: Improving the topological resilience of mobile ad hoc networks. In: 7th International Workshop on Design of Reliable Communication Networks (DRCN), pp. 191–197 (October 2009)
Kim, T., Tipper, D., Krishnamurthy, P.: Connectivity and critical point behavior in mobile ad hoc and sensor networks. In: IEEE Symposium on Computers and Communications, ISCC, pp. 153–158. IEEE (2009)
Kriesell, M.: Minimal connectivity. In: Beineke, L.W., Wilson, R.J. (eds.) Topics in Structural Graph Theory, pp. 71–99. Cambridge University Press (2012)
Newman, M.E.J.: Scientific collaboration networks. ii. shortest paths, weighted networks, and centrality. Phys. Rev. E 64(1), 16132 (2001)
Nicol, D.M., Sanders, W.H., Trivedi, K.S.: Model-based evaluation: From dependability to security. IEEE Transactions on Dependable and Secure Computing 01(1), 48–65 (2004)
Opsahl, T., Agneessens, F., Skvoretz, J.: Node centrality in weighted networks: Generalizing degree and shortest paths. Social Networks 32(3), 245–251 (2010)
Scellato, S., Leontiadis, I., Mascolo, C., Basu, P., Zafer, M.: Evaluating temporal robustness of mobile networks. IEEE Transactions on Mobile Computing 12(1), 105–117 (2013)
Shen, S., Smith, J.C.: Polynomial-time algorithms for solving a class of critical node problems on trees and series-parallel graphs. Networks 60(2), 103–119 (2012)
Sterbenz, J.P.G., Hutchison, D., Çetinkaya, E.K., Jabbar, A., Rohrer, J.P., Schöller, M., Smith, P.: Resilience and survivability in communication networks: Strategies, principles, and survey of disciplines. Computer Networks 54(8), 1245–1265 (2010)
Sterbenz, J.P.G., Krishnan, R., Hain, R.R., Jackson, A.W., Levin, D., Ramanathan, R., Zao, J.: Survivable mobile wireless networks: issues, challenges, and research directions. In: Proceedings of the 3rd ACM workshop on Wireless Security (WiSE), Atlanta, GA, pp. 31–40 (2002)
Tang, J., Musolesi, M., Mascolo, C., Latora, V.: Temporal distance metrics for social network analysis. In: Proceedings of the 2nd ACM Workshop on Online Social Networks, pp. 31–36 (2009)
Zhang, D., Gogi, S.A., Broyles, D.S., Çetinkaya, E.K., Sterbenz, J.P.: Modelling Attacks and Challenges to Wireless Networks. In: Proceedings of the 4th IEEE/IFIP International Workshop on Reliable Networks Design and Modeling (RNDM), pp. 806–812. St. Petersburg (October 2012)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2014 IFIP International Federation for Information Processing
About this paper
Cite this paper
Zhang, D., Sterbenz, J.P.G. (2014). Modelling Critical Node Attacks in MANETs. In: Elmenreich, W., Dressler, F., Loreto, V. (eds) Self-Organizing Systems. IWSOS 2013. Lecture Notes in Computer Science, vol 8221. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-54140-7_11
Download citation
DOI: https://doi.org/10.1007/978-3-642-54140-7_11
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-54139-1
Online ISBN: 978-3-642-54140-7
eBook Packages: Computer ScienceComputer Science (R0)