Abstract
Wireless Sensor Networks (WSN) consist of low powered and resource constrained sensor nodes which are left unattended for long duration of time. Hence it is very challenging to design and implement cost effective security protocols for such networks. Thus symmetric key cryptographic techniques are preferred over public key techniques for communication in such scenarios. Prior to deployment, keys are usually predistributed into the nodes and this problem has been well studied. Highlighting that connectivity and communication are two separate aspects of a WSN, we propose a secure connectivity model using Reed Muller codes. The model is then utilized to securely establish communication keys and exchange messages in a WSN designed on the basis of a scheme that uses affine planes for key predistribution. Novel combination of both the ideas yields highly resilient communication model with full connectivity between nodes.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Bag. S., Ruj, S.: Key Distribution in Wireless Sensor Networks using Finite Affine Plane. In: AINA (2011) (accepted for Publication)
Çamtepe, S.A., Yener, B.: Key distribution mechanisms for wireless sensor networks:A survey 2005. Technical Report. In: TR-05-07 Rensselaer Polytechnic Institute, Computer Science Department (March 2005)
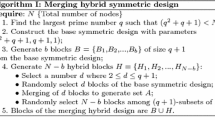
Chakrabarti, D., Maitra, S., Roy, B.: A key pre-distribution scheme for wireless sensor networks: merging blocks in combinatorial design. International Journal of Information Security 5(2), 105–114 (2006)
Cooke, B.: Reed Muller Error Correcting Codes. MIT Undergraduate J. of Mathematics(1999)
Eschenauer, L., Gligor, V.D.: A key-management scheme for distributed sensor networks. In: ACM Conference on Computer and Communications Security, pp. 41–47 (2002)
Gura, N., Patel, A., Wander, A., Eberle, H., Shantz, S.C.: Comparing Elliptic Curve Cryptography and RSA on 8-bit CPUs. In: Joye, M., Quisquater, J.-J. (eds.) CHES 2004. LNCS, vol. 3156, pp. 119–132. Springer, Heidelberg (2004)
Lee, J.-Y., Stinson, D.R.: Deterministic key predistribution schemes for distributed sensor networks. In: Handschuh, H., Hasan, M.A. (eds.) SAC 2004. LNCS, vol. 3357, pp. 294–307. Springer, Heidelberg (2004)
Lee, J.Y., Stinson, D.R.: A combinatorial approach to key predistribution for distributed sensor networks. In: IEEE Wireless Communications and Networking Conference, WCNC 2005, New Orleans, LA, USA (2005)
Ruj, S., Roy, B.: Key predistribution using partially balanced designs in wireless sensor networks. In: Stojmenovic, I., Thulasiram, R.K., Yang, L.T., Jia, W., Guo, M., de Mello, R.F. (eds.) ISPA 2007. LNCS, vol. 4742, pp. 431–445. Springer, Heidelberg (2007)
Ruj, S., Roy, B.: Revisiting key predistribution using transversal designs for a grid-based deployment scheme. In: International Journal of Distributed Sensor Networks IJDSN 2009, vol. 5(6), pp. 660–674 (2009)
Steiner, J.G., Neuman, B.C., Schiller, J.I.: Kerberos: An authentication service for open network systems. USENIX Winter, 191–202 (1988)
Sarkar., P., Saha, A., Chowdhury, M.U.: Secure Connectivity Model in Wireless Sensor Networks Using First Order Reed-Muller Codes. In: MASS 2010, pp. 507–512 (2010)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2011 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Bag, S., Saha, A., Sarkar, P. (2011). Highly Resilient Communication Using Affine Planes for Key Predistribution and Reed Muller Codes for Connectivity in Wireless Sensor Network. In: Özcan, A., Zizka, J., Nagamalai, D. (eds) Recent Trends in Wireless and Mobile Networks. CoNeCo WiMo 2011 2011. Communications in Computer and Information Science, vol 162. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-21937-5_9
Download citation
DOI: https://doi.org/10.1007/978-3-642-21937-5_9
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-21936-8
Online ISBN: 978-3-642-21937-5
eBook Packages: Computer ScienceComputer Science (R0)