Abstract
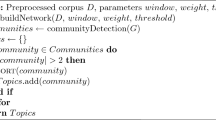
This paper addresses the problem of detecting access to off-topic documents by exploiting user profiles. Existing methods usually store a few prototype off-topic documents as the profile and label their top nearest neighbors in the test set as suspects. This is based on the common assumption that nearby documents are from the same class. However, due to the inherent sparseness of high-dimensional space, a document and its nearest neighbors may not belong to the same class. To this end, we develop a hyperclique pattern based off-topic detection method for selecting which ones to label. Hyperclique patterns consider joint similarity among a set of objects instead of the traditional pairwise similarity. As a result, the objects from hypercliques are more reliable as seeds for classifying their neighbors. Indeed, our experimental results on real world document data favorably demonstrate the effectiveness of our technique over the existing methods in terms of detection precision.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Dept. of Justice of United States: Press releases (2006), http://www.usdoj.gov/criminal/cybercrime/
Kumar, S., Spafford, E.H.: A pattern matching model for misuse intrusion detection. In: Proc. the 17th National Computer Security Conf., pp. 11–21 (1994)
Liao, Y., Vemuri, V.R.: Using text categorization techniques for intrusion detection. In: Proc. of the 11th USENIX Security Symp., pp. 51–59 (2002)
Chung, C.Y., Gertz, M., Levitt, K.: DEMIDS: A misuse detection system for database systems. In: Proc. the 3rd Int. IFIP TC-11 WG11.5 Working Conf. Integrity and Internal Control in Information Systems, pp. 159–178 (1999)
Goharian, N., Platt, A.: Detection using clustering query results. In: Proc. IEEE Int. Conf. Intelligence and Security Informatics, pp. 671–673 (2006)
Goharian, N., Ma, L.: On off-topic access detection in information systems. In: Proc. ACM CIKM, pp. 353–354 (2005)
Cathey, R., Ma, L., Goharian, N., Grossman, D.A.: Misuse detection for information retrieval systems. In: Proc. ACM CIKM, pp. 183–190 (2003)
Breunig, M.M., Kriegel, H.P., Ng, R.T., Sander, J.: LOF: Identifying density-based local outliers. In: Proc. ACM SIGMOD, pp. 93–104 (2000)
Ramaswamy, S., Rastogi, R., Shim, K.: Efficient algorithms for mining outliers from large data sets. In: Proc. ACM SIGMOD, pp. 427–438 (2000)
**ong, H., Tan, P.N., Kumar, V.: Mining strong affinity association patterns in data sets with skewed support distribution. In: Proc. IEEE ICDM, pp. 387–394 (2003)
Huang, Y., **ong, H., Wu, W., Zhang, Z.: A hybrid approach for mining maximal hyperclique patterns. In: Proc. IEEE ICTAI, pp. 354–361 (2004)
Aggarwal, C.C., Yu, P.S.: Outlier detection for high dimensional data. In: Proc. ACM SIGMOD, pp. 37–46 (2001)
Author information
Authors and Affiliations
Editor information
Rights and permissions
Copyright information
© 2007 Springer Berlin Heidelberg
About this paper
Cite this paper
Hu, T., Xu, Q., Yuan, H., Hou, J., Qu, C. (2007). Hyperclique Pattern Based Off-Topic Detection. In: Dong, G., Lin, X., Wang, W., Yang, Y., Yu, J.X. (eds) Advances in Data and Web Management. APWeb WAIM 2007 2007. Lecture Notes in Computer Science, vol 4505. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-72524-4_40
Download citation
DOI: https://doi.org/10.1007/978-3-540-72524-4_40
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-72483-4
Online ISBN: 978-3-540-72524-4
eBook Packages: Computer ScienceComputer Science (R0)