Abstract
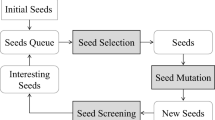
Fuzzing is a popular and effective automatic vulnerability mining method. More and more fuzzing techniques are starting to integrate reinforcement learning. But traditional fuzzing based on reinforcement learning is blind in sample mutation due to the lack of format information and efficient mutation algorithms. As a result, it is challenging to achieve higher coverage and the number of effective fuzzing is limited, leading to low utilization. To mitigate these problems, this paper proposes a new fuzzer named XRLFuzz, a format information guided fuzzing based on deep reinforcement learning for binaries. We use dynamic instrumentation techniques to provide runtime information, And then we use these information to perform format division and extract keywords based on the invalid mutation reuse algorithm. Format information is incorporated into the action dimension of deep reinforcement learning to guide the selection of mutation strategy. The experimental results show that the format division technology and keyword extraction technology both improve the efficiency of fuzzing, and XRLFuzz achieves code coverage of 106% to 276% of AFL.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Miller, B.P., Fredriksen, L., So, B.: An empirical study of the reliability of UNIX utilities. Commun. ACM 33, 32–44 (1990)
Zalewski, M.: American Fuzzy Lop (2019). https://github.com/Google/AFL. Accessed 10 Sep 2019
Fioraldi, A., Maier, D., Eißfeldt, H., et al.: AFL++: combining incremental steps of fuzzing research. In: 14th USENIX Workshop on Offensive Technologies (WOOT 20) (2020)
Eddington, M.: Peach fuzzing platform. http://community.peachfuzzer.com/WhatIsPeach.html
Hasselt, H.: Double Q-learning. Adv. Neural. Inf. Process. Syst. 23, 2613–2621 (2010)
A competitive framework for fuzzing and learning. ar**v preprint ar**v:1807.07490 (2018)
Böhme, M., Pham, V.T., Roychoudhury, A.: Coverage-based Greybox fuzzing as Markov chain. IEEE Trans. Softw. Eng. 45, 489–506 (2017)
Pham, V., Boehme, M., Santosa, A.E., Caciulescu, A.R., Roychoudhury, A.: Smart Greybox fuzzing. IEEE Trans. Softw. Eng. (2019). https://doi.org/10.1109/TSE.2019.2941681
Lyu, C., Ji, S., Li, Y., et al.: SmartSeed: smart seed generation for efficient fuzzing (2018)
Son, S., Lee, S., Han, H., et al.: Montage: a neural network language model-guided Javascript fuzzer. In: 20th USENIX Security Symposium (USENIX Security 2020) (2020)
Zong, P., Lv, T., Wang, D., et al.: FuzzGuard: filtering out unreachable inputs in directed grey-box fuzzing through deep learning. In: 29th USENIX Security Symposium (USENIX Security 20), pp. 2255–2269 (2020)
Böhme, M., Pham, V.T., Nguyen, M.D., et al.: Directed Greybox fuzzing. In: Proceedings of the. ACM SIGSAC Conference on Computer and Communications Security, pp. 2329–2344 (2017)
Vykov, D.: Syzkaller. https://github.com/google/syzkaller (2016)
Lillicrap, T.P., Hunt, J.J., et al.: Continuous control with deep reinforcement learning. ar**v preprint ar**v:1509.02971 (2015)
Serebryany, K.: LibFuzzer-a library for coverage-guided fuzz testing. LLVM project (2015)
Zhang, Z., Cui, B., Chen, C.: Reinforcement learning-based fuzzing technology. In: Barolli, L., Poniszewska-Maranda, A., Park, H. (eds.) IMIS 2020. AISC, vol. 1195, pp. 244–253. Springer, Cham (2021). https://doi.org/10.1007/978-3-030-50399-4_24
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2024 The Author(s), under exclusive license to Springer Nature Switzerland AG
About this paper
Cite this paper
Liu, R., Cui, B., Chen, C., Ma, J. (2024). XRLFuzz: Fuzzing Binaries Guided by Format Information Based on Deep Reinforcement Learning. In: Barolli, L. (eds) Advances in Internet, Data & Web Technologies. EIDWT 2024. Lecture Notes on Data Engineering and Communications Technologies, vol 193. Springer, Cham. https://doi.org/10.1007/978-3-031-53555-0_29
Download citation
DOI: https://doi.org/10.1007/978-3-031-53555-0_29
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-031-53554-3
Online ISBN: 978-3-031-53555-0
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)