Abstract
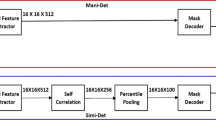
To reduce the difficulty of image forensics on forgery images, in this paper, we present an efficient end-to-end deep learning approach using Residual Structure and Attention Mechanism (RA-Net) for image copy-move forgery detection (CMFD). The RA-Net can locate the forged areas and corresponding genuine areas, and it is composed of two modules, Residual Feature Extraction module (RFEM) and Feature Matching & Up-sampling module (FMUM). RFEM is designed to extract deep feature maps, which enriches the combination of gradient information and attention mechanism that focuses the attention of RA-Net to the forged areas. The FMUM assists RA-Net is used to detect copy-move forgery areas and return the previous output to the size of the input image for analysis and visualization of the results. Furthermore, we create a RANet-CMFD dataset for the training, the way to generate RA-Net-CMFD dataset could help solve the problem of not having enough dataset in some research areas. Otherwise, comparison results show that our model can achieve satisfied performance on CoMoFoD dataset at the pixel level, and performs superior than the compared methods.
This work was supported by the National Natural Science Foundation of China (Grant No. 61902448), the Science and Technology Development Fund of Macau SAR (Grant number 0045/2022/A), and the Research project of the Macao Polytechnic University (Project No. RP/FCA-12/2022).
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Amerini, I., Ballan, L., Caldelli, R., Del Bimbo, A., Serra, G.: A sift-based forensic method for copy-move attack detection and transformation recovery. IEEE Trans. Inf. Forensics Secur. 6(3), 1099–1110 (2011)
Bochkovskiy, A., Wang, C.Y., Liao, H.Y.M.: YOLOv4: optimal speed and accuracy of object detection. ar**v preprint ar**v:2004.10934 (2020)
Cozzolino, D., Poggi, G., Verdoliva, L.: Efficient dense-field copy-move forgery detection. IEEE Trans. Inf. Forensics Secur. 10(11), 2284–2297 (2015)
Fridrich, J., Kodovsky, J.: Rich models for steganalysis of digital images. IEEE Trans. Inf. Forensics Secur. 7(3), 868–882 (2012)
Huang, H., Guo, W., Zhang, Y.: Detection of copy-move forgery in digital images using sift algorithm. In: 2008 IEEE Pacific-Asia Workshop on Computational Intelligence and Industrial Application, vol. 2, pp. 272–276. IEEE (2008)
Kakar, P., Sudha, N.: Exposing postprocessed copy-paste forgeries through transform-invariant features. IEEE Trans. Inf. Forensics Secur. 7(3), 1018–1028 (2012)
Khotanzad, A., Hong, Y.H.: Invariant image recognition by Zernike moments. IEEE Trans. Pattern Anal. Mach. Intell. 12(5), 489–497 (1990)
Koul, S., Kumar, M., Khurana, S.S., Mushtaq, F., Kumar, K.: An efficient approach for copy-move image forgery detection using convolution neural network. Multimed. Tools Appl. 81(8), 11259–11277 (2022)
Li, J., Li, X., Yang, B., Sun, X.: Segmentation-based image copy-move forgery detection scheme. IEEE Trans. Inf. Forensics Secur. 10(3), 507–518 (2014)
Lin, T.-Y., et al.: Microsoft COCO: common objects in context. In: Fleet, D., Pajdla, T., Schiele, B., Tuytelaars, T. (eds.) ECCV 2014. LNCS, vol. 8693, pp. 740–755. Springer, Cham (2014). https://doi.org/10.1007/978-3-319-10602-1_48
Mishra, P., Mishra, N., Sharma, S., Patel, R., et al.: Region duplication forgery detection technique based on surf and HAC. Sci. World J. 2013 (2013)
Rao, Y., Ni, J.: A deep learning approach to detection of splicing and copy-move forgeries in images. In: 2016 IEEE International Workshop on Information Forensics and Security (WIFS), pp. 1–6. IEEE (2016)
Ryu, S.J., Kirchner, M., Lee, M.J., Lee, H.K.: Rotation invariant localization of duplicated image regions based on Zernike moments. IEEE Trans. Inf. Forensics Secur. 8(8), 1355–1370 (2013)
Ryu, S.-J., Lee, M.-J., Lee, H.-K.: Detection of copy-rotate-move forgery using Zernike moments. In: Böhme, R., Fong, P.W.L., Safavi-Naini, R. (eds.) IH 2010. LNCS, vol. 6387, pp. 51–65. Springer, Heidelberg (2010). https://doi.org/10.1007/978-3-642-16435-4_5
Silva, E., Carvalho, T., Ferreira, A., Rocha, A.: Going deeper into copy-move forgery detection: exploring image telltales via multi-scale analysis and voting processes. J. Vis. Commun. Image Represent. 29, 16–32 (2015)
Simonyan, K., Zisserman, A.: Very deep convolutional networks for large-scale image recognition. ar**v preprint ar**v:1409.1556 (2014)
Tralic, D., Zupancic, I., Grgic, S., Grgic, M.: CoMoFoD-new database for copy-move forgery detection. In: Proceedings ELMAR-2013, pp. 49–54. IEEE (2013)
Wang, C.Y., Liao, H.Y.M., Wu, Y.H., Chen, P.Y., Hsieh, J.W., Yeh, I.H.: CSPNet: a new backbone that can enhance learning capability of CNN. In: Proceedings of the IEEE/CVF Conference on Computer Vision and Pattern Recognition Workshops, pp. 390–391 (2020)
Wang, J., Liu, G., Zhang, Z., Dai, Y., Wang, Z.: Fast and robust forensics for image region-duplication forgery. Acta Automatica Sinica 35(12), 1488–1495 (2009)
Wen, B., Zhu, Y., Subramanian, R., Ng, T.T., Shen, X., Winkler, S.: Coverage-a novel database for copy-move forgery detection. In: 2016 IEEE International Conference on Image Processing (ICIP), pp. 161–165. IEEE (2016)
Wu, Y., Abd-Almageed, W., Natarajan, P.: BusterNet: detecting copy-move image forgery with source/target localization. In: Proceedings of the European Conference on Computer Vision (ECCV), pp. 168–184 (2018)
**ao, J., Hays, J., Ehinger, K.A., Oliva, A., Torralba, A.: Sun database: large-scale scene recognition from abbey to zoo. In: 2010 IEEE Computer Society Conference on Computer Vision and Pattern Recognition, pp. 3485–3492. IEEE (2010)
Acknowledgements
This work was supported by the National Natural Science Foundation of China (Grant No. 61902448), the Science and Technology Development Fund of Macau SAR (Grant number 0045/2022/A), and the Research project of the Macao Polytechnic University (Project No. RP/FCA-12/2022).
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2023 The Author(s), under exclusive license to Springer Nature Switzerland AG
About this paper
Cite this paper
Zhao, K., Yuan, X., **e, Z., Huang, G., Feng, L. (2023). RA-Net: A Deep Learning Approach Based on Residual Structure and Attention Mechanism for Image Copy-Move Forgery Detection. In: Iliadis, L., Papaleonidas, A., Angelov, P., Jayne, C. (eds) Artificial Neural Networks and Machine Learning – ICANN 2023. ICANN 2023. Lecture Notes in Computer Science, vol 14263. Springer, Cham. https://doi.org/10.1007/978-3-031-44204-9_31
Download citation
DOI: https://doi.org/10.1007/978-3-031-44204-9_31
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-031-44203-2
Online ISBN: 978-3-031-44204-9
eBook Packages: Computer ScienceComputer Science (R0)