Abstract
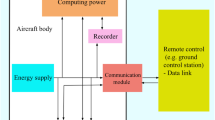
To address the threats of consumer drones, effective drone countermeasures are required. As with such a process, identifying the specific type of invading drone is the critical initial step. While existing drone identification systems show some advantages, they also have several limitations, such as cost and deployability. In this paper, a unique method is proposed to identify drones based on features in the encrypted traffic between a drone and its controller. These features are constructed based on an in-depth understanding of drone communication protocols, which aids in classifying different types of popular ArduPilot drones. We collected plaintext and encrypted traffic from multiple drones, analyzed their communication patterns, and extracted features to identify specific drones. The experimental results show that the proposed framework can precisely identify target drones while outperforming existing methods. While this paper focuses on drone communications, the proposed method can also be applied to classify many other auto-control devices that exhibit similar communication behaviors.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
ArduPilot Documentation (2016). https://ardupilot.org/ardupilot
Koubaa, A., Allouch, A., Alailan, M., Javed, Y., Belghith, A., Khalgui, M.: Micro air vehicle link (MAVLink) in a nutshell: a survey. IEEE Access 7, 87658–87680 (2019)
How CCMP is used in RSN (2008). http://etutorials.org/networking
Liang, D.: Identifying consumer drones via encrypted traffic. M.S. thesis, University of Hawaii at Manoa (2022).
Ardupilot-Solo (2013). https://github.com/3drobotics/ardupilot-solo
Alipour-Fanid, A., Dabaghchian, M., Wang, N., Wang, P., Zhao, L., Zeng, K.: Machine learning-based delay-aware UAV detection and operation mode identification over encrypted WiFi traffic. IEEE Trans. Info. Forensic Security 15, 2346–2360 (2020)
Bisio, I., Garibotto, C., Lavagetto, F., Levorato, M., Sciarrone, A.: Statistical analysis of wireless traffic: an adversarial approach to drone surveillance. In: 2019 IEEE Global Communications Conference (GLOBECOM), pp. 1–6 (2019)
Rezaei, S., Liu, X.: Deep learning for encrypted traffic classification: an overview. IEEE Commun. Mag. 57(5), 76–81 (2019)
DroneKit-Python API Guide (2015). https://dronekit-python.readthedocs.io/en/latest/guide
Aircrack-ng (2009). http://aircrack-ng.org
Singh, R. R., Moreira, J., Chothia, T., Ryan, M. D.: Modelling of 802.11 4-way handshake attacks and analysis of security properties. In: Markantonakis, K., Petrocchi, M. (eds) Security and Trust Management. STM 2020. Lecture Notes in Computer Science, p. 12386 (2020)
Dickey, D., Fuller, W.: Distribution of the estimators for autoregressive time series with a unit root. J. Am. Stat. Assoc. 74, 366–427 (1979).
Vijaymeena, M.K., Kavitha, K.: A survey on similarity measures in text mining. Mach. Learn. Appl. Int. J. 3(1), 22 (2016)
Pedregosa, F.: Scikit-learn: machine learning in Python. JMLR 12, 2825–2830 (2011)
Hosmer Jr., D. W., Lemeshow, S., Sturdivant: R. X.: Applied Logistic Regression. John Wiley & Sons, Inc., Hoboken, New Jersey (2013).
Fan, R.-E., Chang, K.-W., Hsieh, C.-J., Wang, X.-R., Lin, C.-J.: LIBLINEAR: a library for large linear classification. J. Mach. Learn. Res. 9, 1871–1874 (2008)
Morales, J. L., Nocedal, J.: L-BFGS-B: Remark on Algorithm 778: L-BFGS-B, FORTRAN routines for large scale bound constrained optimization. ACM Trans. Math. Softw. 38(1), 1–4 (2011)
Defazio, A., Bach, F., Lacoste-Julien, S.: SAGA: a fast incremental gradient method with support for non-strongly convex composite objectives. Adv. Neural Inform. Process. Syst. 27, 1646–1654 (2014).
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2024 The Author(s), under exclusive license to Springer Nature Switzerland AG
About this paper
Cite this paper
Liang, D., Dong, Y. (2024). Identifying Consumer Drones via Encrypted Traffic. In: Azimov, D. (eds) Proceedings of the IUTAM Symposium on Optimal Guidance and Control for Autonomous Systems 2023. IUTAM 2023. IUTAM Bookseries, vol 40. Springer, Cham. https://doi.org/10.1007/978-3-031-39303-7_5
Download citation
DOI: https://doi.org/10.1007/978-3-031-39303-7_5
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-031-39302-0
Online ISBN: 978-3-031-39303-7
eBook Packages: EngineeringEngineering (R0)