Abstract
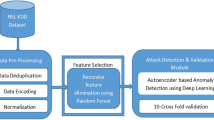
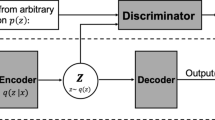
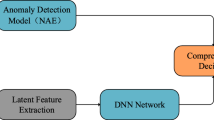
Anomaly detection in network traffic with the high-volume and rapidity is a challenging. Data arrives along with the time with latent distribution changes lead to a single stationary model that doesn’t match streaming data all the time. Therefore, it is necessary to maintain a dynamic system to adapt to changes in the network environment. In solving that problem, supervised learning methods have attracted extensive attention for their capability to detect attacks known as anomalies. However, they require a large amount of labeled training data to train an effective model, which is difficult and expensive to obtain. In this paper, we propose to use LSTM Auto-encoder to extract temporal features from different sequences of network packets that are unlabeled or partially labeled data. After obtaining good data representation, the feedforward neural networks are applied to perform the identification of network traffic anomalies. Our experimental results with the ISCX-IDS-2012 dataset show that our work obtains high performance in intrusion detection with accuracy approximately 99%.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
LeCun, Y., Bengio, Y., Hinton, G.: Deep learning. Nat. Int. J. Sci. 521, 436–444 (2015)
Klaus, G., Rupesh, K.S., Jan, K., et al.: LSTM - a search space odyssey. Trans. Neural Netw. Learn. Syst. 28(10), 2222–2232 (2017)
Cho, K., Van Merriënboer, B., Gulcehre, C., Bahdanau, D., Bougares, F., Schwenk, H., Bengio, Y.: Learning Phrase Representations using RNN Encoder-Decoder for Statistical Machine Translation, ar** a systematic approach to generate benchmark datasets for intrusion detection. Comput. Secur. 31(3), 357–374 (2012)
Chandola, V., Banerjee, A., Kumar, V.: Anomaly detection: a survey. ACM Comput. Surv. 41(3), 1–58 (2009)
Davis, J.J., Clark, A.J.: Data preprocessing for anomaly based network intrusion detection: a review. Comput. Secur. 30(6–7), 353–375 (2011)
Ahmadi, M., Ulyanov, D., Semenov, S., Trofimov, M., Giacinto, G.: Novel feature extraction, selection and fusion for effective malware family classification. In: 6th ACM Conference on Data and Application Security and Privacy (2016)
Bhattacharyya, D.K., Kalita, J.K.: Network Anomaly Detection-A Machine Learning Perspective. CRC Press, Taylor & Francis Group (2014)
Bengio, Y., Lamblin, P., Popovici, D., Larochelle, H.: Greedy layer-wise training of deep networks. In: Advances in Neural Information Processing Systems 19 (2006)
Zhou, G., Sohn, K., Lee, H.: Online incremental feature learning with denoising autoencoders. In: the 15th International Conference on Artificial Intelligence and Statistics (AISTATS) (2012)
Mirsky, Y., Doitshman, T., Elovici, Y., Shabtai, A.: Kitsune: an ensemble of autoencoders for online NID. In: Network and Distributed Systems Security Symposium (NDSS), San Diego, CA, USA (2018)
Niyaz, Q., Sun, W., Javaid, A., Alam, M.: A deep learning approach for NIDS. In: Bio-inspired Information and Communications Technologies, (BIONETICS), Brussels, Belgium (2014)
Yousefi-Azar, M., Varadharajan, V., Hamey, L., Tupakula, U.: Autoencoder-based feature learning for cyber security applications. In: International Joint Conference on Neural Networks (IJCNN), Anchorage, AK, USA (2017)
Farahnak, F., Heikkonen, J.: A deep auto-encoder based approach for IDS. In: International Conference on Advanced Communications Technology (ICACT), Korea (2018)
Srivastava, N., Mansimov, E., Salakhutdinov, R.: Unsupervised learning of video representations using LSTMs. In: 32nd International Conference on Machine, France (2015)
Zhang, Z., Ringeval, F., Han, J., Deng, J., Marchi, E., et al.: Facing realism in spontaneous emotion recognition from speech: feature enhancement by autoencoder with LSTM. In: 17th Annual Conference of the International Speech, INTERSPEECH, San Francisco, CA, US (2016)
Mehdiyeva, N., Lahanna, J., Emricha, A., Enkeb, D., Fettkea, P., Loosa, P.: Time series classification using deep learning for process planning: a case from the process industry. In: the Complex Adaptive Systems Conference with Theme: Engineering Cyber Physical Systems, Chicago, Illinois, USA (2017)
Abadi, M., et al.: TensorFlow: large-scale machine learning on heterogeneous distributed systems, March 2016. https://arxiv.org/abs/1603.04467
Mirza, A.H., Cosan, S.: Computer network intrusion detection using sequential LSTM neural networks autoencoders. In: 26th Signal Processing and Communications Applications Conference (SIU), Izmir, Turkey (2018)
Tan, Z., Jam, A., He, X., Nanda, P., Liu, R., Hu, J.: Detection of dos attacks based on computer vision techniques. IEEE Trans. Comput. 64(9), 15 (2015)
Kumar, G., Kumar, K.: Design of an evolutionary approach for intrusion, vol. 2013, p. 14. Hindawi Publishing Corporation (2013)
Yassin, W., Udzir, N., Muda, Z., Sulaiman, M.: Anomaly-based intrusion detection through Kmeans clustering and Naives Bayes classification. In: International Conference on Computing and Informatics (ICOCI), Malaysia (2013)
Li, C., Wang, J., Ye, X.: Using a recurrent neural network and restricted boltzmann machines for malicious traffic detection. NeuroQuantology 16(5), 823–831 (2018)
Wang, W., Sheng, Y., Wang, J.: HAST-IDS: learning hierarchical spatial-temporal features using DNNs to improve intrusion detection. IEEE Access 6, 1792–1806 (2018)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2021 The Editor(s) (if applicable) and The Author(s), under exclusive license to Springer Nature Switzerland AG
About this paper
Cite this paper
Van, N.T., Sach, L.T., Thinh, T.N. (2021). Temporal Features Learning Using Autoencoder for Anomaly Detection in Network Traffic. In: Huang, YP., Wang, WJ., Quoc, H.A., Giang, L.H., Hung, NL. (eds) Computational Intelligence Methods for Green Technology and Sustainable Development. GTSD 2020. Advances in Intelligent Systems and Computing, vol 1284. Springer, Cham. https://doi.org/10.1007/978-3-030-62324-1_2
Download citation
DOI: https://doi.org/10.1007/978-3-030-62324-1_2
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-62323-4
Online ISBN: 978-3-030-62324-1
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)