Abstract
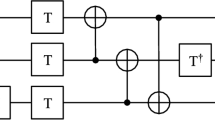
With the continuous advancement of quantum technologies, the estimation of quantum resources necessary for quantum tasks becomes extremely important for optimization purpose. Quantum resource estimation approximates the amount of qubits, time, and the number of quantum gates required to complete a quantum computation. The difficulties in estimating quantum resources result the complexity of quantum systems. Precise estimates can be difficult because of the non-linear behaviour, entanglement effects, and resource limitations that might occur in quantum calculations. In this paper, the symmetric key cryptographic algorithms, PRINCE and Midori block ciphers are converted into the quantum circuit which will be used for applying Grover’s algorithm for exhaustive key search that reduces its security level from \(2^n\) bits to \(2^{\frac{n}{2}}\) bits. This paper discusses the construction of a quantum circuit for a substitution box (or S-box) using two level unitary matrix. The construction of substitution boxes in simple block ciphers as quantum circuits has lately been the subject of several publications, but they are limited to only 4-bit. A substitution box of size \(2^n\) bit, where n is a natural number, is converted into a quantum circuit using the two-level unitary matrix method.









Similar content being viewed by others
Data availability
Not applicable.
References
Atzori L, Iera A, Morabito G (2010) The Internet of Things: a survey. Comput Netw 54(15):2787–2805. https://doi.org/10.1016/j.comnet.2010.05.010
Biryukov A, Perrin L (2023) State of the art in lightweight symmetric cryptography, cryptology ePrint Archive, 2017. https://eprint.iacr.org/2017/511. Accessed 10 Jan
Borghoff J et al (2012) PRINCE—a low-latency block cipher for pervasive computing applications. Adv Cryptol ASIACRYPT 2012:208–225. https://doi.org/10.1007/978-3-642-34961-4_14
Banik S et al (2015) Midori: a block cipher for low energy. Adv Cryptol ASIACRYPT 2015:411–436. https://doi.org/10.1007/978-3-662-48800-3_17
Yasmin N, Gupta R (2023) Modified lightweight GIFT cipher for security enhancement in resource-constrained IoT devices. Int J Inf Technol. https://doi.org/10.1007/s41870-023-01439-9
Sivakumar A, Sriwastawa A, Muthalagu R (2023) Shakey: an improved cipher for protection of Iot devices. Int J Inf Technol 15:3381–3390. https://doi.org/10.1007/s41870-023-01402-8
Bhoyar P, Sahare P, Hashmi M, Dhok S, Deshmukh R (2024) Lightweight architecture for fault detection in Simeck cryptographic algorithms on FPGA. Int J Inf Technol 16:337–343. https://doi.org/10.1007/s41870-023-01593-0
Deepthi Kakumani K, Singh K (2022) Improved related-cipher attack on Salsa and ChaCha: revisited. Int J Inf Technol 14:1535–1542. https://doi.org/10.1007/s41870-022-00904-1
Anne C et al (2019) Saturnin—a suite of lightweight symmetric algorithms for post-quantum security. https://Project.inria.fr/Saturnin/
Allu SN, Naidu TA, Rao KG (2024) Optimized quantum circuit implementation of SATURNIN for Grover algorithm. Int J Inf Technol. https://doi.org/10.1007/s41870-024-01792-3
Grover LK (1996) A fast quantum mechanical algorithm for database search. ar**v:quant-ph/9605043
Amento-Adelmann B, Grassl M, Langenberg B, Liu Y.K, Schoute E, Steinwandt R (2018) Quantum cryptanalysis of block ciphers: a case study. In: Proceedings of the poster at quantum information processing QIP, Delft, The Netherlands, 15–19. https://www.kurims.kyoto-u.ac.jp/~kyodo/kokyuroku/contents/pdf/1166-29.pdf
Jaques S, Naehrig M, Roetteler M, Virdia F (2020) Implementing grover oracles for quantum key search on AES and LowMC. Adv Cryptol EUROCRYPT 2020:280–310. https://doi.org/10.1007/978-3-030-45724-2_10
Anand R, Maitra A, Mukhopadhyay S (2020) Grover on SIMON. Quant Inf Process 19:9. https://doi.org/10.1007/s11128-020-02844-w
Jang K, Choi S, Kwon H, Kim H, Park J, Seo H (2020) Grover on Korean Block Ciphers. Appl Sci 10(18):6407. https://doi.org/10.3390/app10186407
Song G, Jang K, Kim H, Eum S, Sim M, Kim H, Lee W, Seo H (2022) SPEEDY quantum circuit for Grover’s algorithm. Appl Sci 12:6870. https://doi.org/10.3390/app12146870
Yangru Z, Juntao G, Baocang W (2023) Nested quantum search model on symmetric ciphers and its applications, Cryptology ePrint Archive, Paper 2023/327. https://eprint.iacr.org/2023/327
Da L, **ang Z, Runqing X, Shasha Z, **angyong Z (2023) Optimized quantum implementation of AES. Cryptology ePrint Archive
Nielsen M, Chuang I Quantum computation and quantum information. http://mmrc.amss.cas.cn/tlb/201702/W020170224608149940643.pdf
Borghoff J et al (2012) PRINCE—a low-latency block cipher for pervasive computing applications. Adv Cryptol ASIACRYPT 2012:208–225. https://doi.org/10.1007/978-3-642-34961-4_14
Quantum logic gate, Wikipedia, Feb. 29, (2020) https://en.wikipedia.org/wiki/Quantum_logic_gate. Accessed 20 Feb 2023
Singhal A, Chatterjee A (2018) Grover’s Algorithm. ResearchGate. https://www.researchgate.net/publication/342131364_Grover’s_Algorithm
Jang K, Song G, Kim H, Kwon H, Kim H, Seo H (2021) Efficient implementation of PRESENT and GIFT on quantum computers. Appl Sci 11(11):4776. https://doi.org/10.3390/app11114776
Dmytro F (2019) Decomposition of unitary matrix into quantum gates, 8.06x Physical Review, June
Denisenko DV (2019) Quantum circuits for S-box implementation without ancilla qubits. J Exp Theor Phys 128(6):847–855
GitHub. (n.d.). S-Box design/sbox creating code at main. AusafHussainAhklaq/S-Box design. [online] Available at: https://github.com/AusafHussainAhklaq/S-Box_design/blob/main/sbox_creating_code. Accessed 11 Jul 2023
Sracic M: Quantum circuits for matrix multiplication, Last updated July 26, 2011. https://www.math.k-state.edu/research/reu/results2011_files/quantumAlgorithms.pdf
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Akhlaq, A.H., Allu, S.N. & Yerukala, N. Quantum resource estimation of PRINCE and Midori Block Ciphers. Int. j. inf. tecnol. (2024). https://doi.org/10.1007/s41870-024-01997-6
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s41870-024-01997-6