Abstract
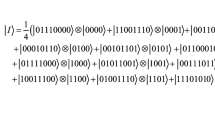
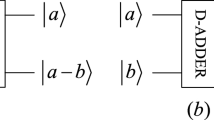
The parallel computing power of quantum computing and the special properties of qubits provide an effective solution for image processing tasks. This paper presents a quantum image encryption algorithm based on Fisher–Yates algorithm and Logistic map**. Firstly, the Fisher–Yates algorithm is used to generate three key sequences, one of which is used to encode the coordinate qubits of the image. Using the other two keys and the preset rules, the quantum coordinate scrambling operation is designed based on the encoded coordinate qubit, which effectively scrambles the spatial information of the plaintext image. Next, another set of key sequences is generated, one of which is used to encode the color qubits of the image. Using two other key sequences and different rules, a qubit plane scrambling operation based on coded color qubits is designed, and the color information of image is scrambled successfully. Finally, the quantum key image is generated based on Logistic map**, and the key image is scrambled based on Fisher–Yates algorithm to improve the key complexity. The final ciphertext image is obtained by performing XOR operation between the original image and the scrambled key image. The complete quantum circuit diagram of the scheme is given in this paper. The experimental results and security analysis prove the effectiveness of the scheme, which provides a large key space and the computational complexity is only O(n).



















Similar content being viewed by others
Data availability
The datasets generated during and/or analyzed during the current study are available from the corresponding author on reasonable request.
References
Liu, S., Guo, C., Sheridan, J.T.: A review of optical image encryption techniques. Opt. Laser Technol. 57, 327–342 (2014)
Ghadirli, H.M., Nodehi, A., Enayatifar, R.: An overview of encryption algorithms in color images. Sig. Process. 164, 163–185 (2019)
Kaur, M., Kumar, V.: A comprehensive review on image encryption techniques. Arch. Comput. Methods Eng. 27, 15–43 (2020)
Alvarez, G., Li, S.: Some basic cryptographic requirements for chaos-based cryptosystems. Int. J. Bifurc. Chaos 16(08), 2129–2151 (2006)
Farah, M.B., Guesmi, R., Kachouri, A., Samet, M.: A novel chaos based optical image encryption using fractional fourier transform and dna sequence operation. Opt. Laser Technol. 121, 105777 (2020)
Hua, Z., Zhu, Z., Chen, Y., Li, Y.: Color image encryption using orthogonal latin squares and a new 2d chaotic system. Nonlinear Dyn. 104, 4505–4522 (2021)
Wang, X., Li, Y.: Chaotic image encryption algorithm based on hybrid multi-objective particle swarm optimization and dna sequence. Opt. Lasers Eng. 137, 106393 (2021)
Gao, X., Mou, J., Banerjee, S., Cao, Y., **ong, L., Chen, X.: An effective multiple-image encryption algorithm based on 3d cube and hyperchaotic map. J. King Saud Univ.-Comput. Inf. Sci. 34(4), 1535–1551 (2022)
Feynman, R.P.: Simulating physics with computers. Int. J. Theor. Phys. 21(6/7) (1982)
Deutsch, D.: Quantum theory, the church-turing principle and the universal quantum computer. Proc. Roy. Soc. Lond. A Math. Phys. Sci. 400(1818), 97–117 (1985)
Shor, P.W.: Algorithms for quantum computation: discrete logarithms and factoring. In: Proceedings 35th Annual Symposium on Foundations of Computer Science, pp. 124–134. Ieee (1994)
Grover, L.K.: A fast quantum mechanical algorithm for database search. In: Proceedings of the Twenty-eighth Annual ACM Symposium on Theory of Computing, pp. 212–219. (1996)
Horodecki, R., Horodecki, P., Horodecki, M., Horodecki, K.: Quantum entanglement. Rev. Mod. Phys. 81(2), 865 (2009)
Venegas-Andraca, S.E., Bose, S.: Storing, processing, and retrieving an image using quantum mechanics. In: Quantum Information and Computation, vol. 5105, pp. 137–147. SPIE (2003)
Latorre, J.I.: Image compression and entanglement. ar**v preprint ar**v:quant-ph/0510031 (2005)
Venegas-Andraca, S.E., Ball, J.: Processing images in entangled quantum systems. Quantum Inf. Process. 9(1), 1–11 (2010)
Le, P.Q., Dong, F., Hirota, K.: A flexible representation of quantum images for polynomial preparation, image compression, and processing operations. Quantum Inf. Process. 10, 63–84 (2011)
Zhang, Y., Lu, K., Gao, Y., Wang, M.: Neqr: a novel enhanced quantum representation of digital images. Quantum Inf. Process. 12, 2833–2860 (2013)
Jiang, N., Wang, J., Mu, Y.: Quantum image scaling up based on nearest-neighbor interpolation with integer scaling ratio. Quantum Inf. Process. 14(11), 4001–4026 (2015)
Sang, J., Wang, S., Li, Q.: A novel quantum representation of color digital images. Quantum Inf. Process. 16, 1–14 (2017)
Wang, L., Ran, Q., Ma, J., Yu, S., Tan, L.: Qrci: a new quantum representation model of color digital images. Opt. Commun. 438, 147–158 (2019)
Khan, R.A.: An improved flexible representation of quantum images. Quantum Inf. Process. 18, 1–19 (2019)
Wang, L., Ran, Q., Ma, J.: Double quantum color images encryption scheme based on dqrci. Multimedia Tools Appl. 79, 6661–6687 (2020)
Wang, B., Hao, M.-Q., Li, P.-C., Liu, Z.-B.: Quantum representation of indexed images and its applications. Int. J. Theor. Phys. 59(2), 374–402 (2020)
Zhang, J., Huang, Z., Li, X., Wu, M., Wang, X., Dong, Y.: Quantum image encryption based on quantum image decomposition. Int. J. Theor. Phys. 60, 2930–2942 (2021)
Gao, Y.-J., **e, H.-W., Zhang, J., Zhang, H.: A novel quantum image encryption technique based on improved controlled alternated quantum walks and hyperchaotic system. Physica A 598, 127334 (2022)
Hao, W., Zhang, T., Chen, X., Zhou, X.: A hybrid neqr image encryption cryptosystem using two-dimensional quantum walks and quantum coding. Sig. Process. 205, 108890 (2023)
Gong, L.-H., He, X.-T., Cheng, S., Hua, T.-X., Zhou, N.-R.: Quantum image encryption algorithm based on quantum image xor operations. Int. J. Theor. Phys. 55, 3234–3250 (2016)
Wang, J., Geng, Y.-C., Han, L., Liu, J.-Q.: Quantum image encryption algorithm based on quantum key image. Int. J. Theor. Phys. 58, 308–322 (2019)
Abd-El-Atty, B., Abd El-Latif, A.A., Venegas-Andraca, S.E.: An encryption protocol for neqr images based on one-particle quantum walks on a circle. Quantum Inf. Process. 18(9), 272 (2019)
Zhou, S.: A quantum image encryption method based on dnacnot. IEEE Access 8, 178336–178344 (2020)
Li, H.-S., Chen, X., Song, S., Liao, Z., Fang, J.: A block-based quantum image scrambling for gneqr. IEEE Access 7, 138233–138243 (2019)
Zhou, R.-G., Li, Y.-B.: Quantum image encryption based on lorenz hyper-chaotic system. Int. J. Quantum Inf. 18(05), 2050022 (2020)
Liu, X., **ao, D., Liu, C.: Three-level quantum image encryption based on arnold transform and logistic map. Quantum Inf. Process. 20, 1–22 (2021)
Hu, M., Li, J., Di, X.: Quantum image encryption scheme based on 2d s ine 2-l ogistic chaotic map. Nonlinear Dyn. 111(3), 2815–2839 (2023)
Durstenfeld, R.: Algorithm 235: random permutation. Commun. ACM 7(7), 420 (1964)
Gilbert, H., Handschuh, H.: Security analysis of sha-256 and sisters. In: International Workshop on Selected Areas in Cryptography, pp. 175–193. Springer (2003)
Liu, H., Zhao, B., Huang, L.: Quantum image encryption scheme using arnold transform and s-box scrambling. Entropy 21(4), 343 (2019)
Hu, W.-W., Zhou, R.-G., Jiang, S., Liu, X., Luo, J.: Quantum image encryption algorithm based on generalized arnold transform and logistic map. CCF Trans. High Perform. Comput. 2, 228–253 (2020)
Guo, L., Du, H., Huang, D.: A quantum image encryption algorithm based on the feistel structure. Quantum Inf. Process. 21, 1–18 (2022)
Funding
This work is supported by the National Natural Science Foundation of China under Grant No. 62062035 and Fujian Provincial Natural Science Foundation Project under Grant No. 2023J011389.
Author information
Authors and Affiliations
Contributions
** Fan and Yiteng Zhang wrote the whole manuscript. All authors reviewed the manuscript.
Corresponding author
Ethics declarations
Conflict of interest
The authors declare that they have no conflict of interest.
Consent to participate
All authors consent to participate.
Consent for publication
All authors consent for publication.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Fan, P., Zhang, Y. Quantum image encryption algorithm based on Fisher–Yates algorithm and Logistic map**. Quantum Inf Process 23, 237 (2024). https://doi.org/10.1007/s11128-024-04441-7
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11128-024-04441-7