Abstract
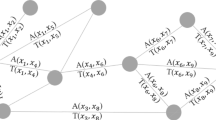
The adoption of blockchain technology within various critical infrastructures is on the rise. Concurrently, there has been a corresponding increase in its misuse, primarily through the exploitation of its pseudo-anonymous characteristic. Encouraging blockchain adoption and improving security in the decentralised environment require techniques to detect wallets and/or smart contracts owned by malicious entities. Illegal activities such as dark market trades, money laundering, and receiving unlawful payments are performed by connecting various wallets or smart contracts in a meticulous way. A graph can be a potential representation to visualise such interconnections via various patterns, and graph-based data may represent the topological structure of the blockchain network. Recently, Graph Neural Networks (GNN) have been widely used for analysing the structure of complex networks and identifying patterns. This is the first work that considers a generalised graph representation for the Bitcoin and Ethereum networks and analyses their behaviour using a combination of heterogeneous GNN framework’s GraphSAGE and Graph Attention Network (GAT). The classification results reveal that the proposed approach modestly improved Bitcoin network analysis, whereas Ethereum smart contract analysis needs further investigation in terms of incorporating other aspects of smart contracts, such as code-base, byte length, and lifetime features.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Blockchain data API (2021). https://www.blockchain.com/api/blockchain_api
Ponzi smart contract (2021). https://www.kaggle.com/datasets/xblock/smart-ponzi-scheme-labels
Ethereum transaction dataset (2022). https://api.blockcypher.com/v1/eth/main/txs/
Jeyakumar, S.T., Ko, R., Muthukkumarasamy, V.: A framework for user-centric visualisation of blockchain transactions in critical infrastructure. In: Proceedings of the 5th ACM International Symposium on Blockchain and Secure Critical Infrastructure (BSCI 2023), pp. 44–52. Association for Computing Machinery, New York, USA (2023). https://doi.org/10.1145/3594556.3594624
Akcora, C.G., Li, Y., Gel, Y.R., Kantarcioglu, M.: Bitcoinheist: topological data analysis for ransomware detection on the bitcoin blockchain. ar**v preprint [Web Link] (2019)
Akoglu, L., Tong, H., Koutra, D.: Graph-based anomaly detection and description: a survey (2014)
Brambilla, M., Javadian Sabet, A., Kharmale, K., Sulistiawati, A.E.: Graph-based conversation analysis in social media. Big Data Cogn. Comput. 6(4) (2022). https://doi.org/10.3390/bdcc6040113, https://www.mdpi.com/2504-2289/6/4/113
Breiman, L.: Random forests. Mach. Learn. 45, 5–32 (2001)
Di Francesco Maesa, D., Mori, P.: Blockchain 3.0 applications survey (2020)
Grover, A., Leskovec, J.: node2vec: Scalable feature learning for networks. In: Proceedings of the 22nd ACM SIGKDD International Conference on Knowledge Discovery and Data Mining, pp. 855–864 (2016)
Hamilton, W.L., Ying, R., Leskovec, J.: Inductive representation learning on large graphs (2018)
He, X., Yang, T., Chen, L.: CTRF: ethereum-based ponzi contract identification. Secur. Commun. Netw. 2022 (2022)
Hearst, M.A., Dumais, S.T., Osuna, E., Platt, J., Scholkopf, B.: Support vector machines. IEEE Intell. Syst. Appl. 13(4), 18–28 (1998)
Jeyakumar, S., Eugene Yugarajah, A.C., Rathore, P., Palaniswami, M., Muthukkumarasamy, V., Hóu, Z.: Feature engineering for anomaly detection and classification of blockchain transactions, March 2023. https://doi.org/10.36227/techrxiv.22329805.v1, https://www.techrxiv.org/articles/preprint/Feature_Engineering_for_Anomaly_Detection_and_Classification_of_Blockchain_Transactions/22329805
Jeyakumar, S., Hóu, Z., Eugene Yugarajah, A.C., Palaniswami, M., Muthukkumarasamy, V.: Visualizing blockchain transaction behavioural pattern: a graph-based approach, March 2023. https://doi.org/10.36227/techrxiv.22329889.v1, https://www.techrxiv.org/articles/preprint/Visualizing_Blockchain_Transaction_Behavioural_Pattern_A_Graph-based_Approach/22329889
Kılıç, B., Özturan, C., Sen, A.: Analyzing large-scale blockchain transaction graphs for fraudulent activities. Big Data Artif. Intell. Digit. Finan. 253 (2022)
Kingma, D.P., Ba, J.: Adam: a method for stochastic optimization (2017)
Kipf, T.N., Welling, M.: Semi-supervised classification with graph convolutional networks (2017)
Kriegel, H.P., Kröger, P., Schubert, E., Zimek, A.: Loop: local outlier probabilities. In: Proceedings of the 18th ACM Conference on Information and Knowledge Management, pp. 1649–1652 (2009)
Lee, C., Maharjan, S., Ko, K., Hong, J.W.-K.: Toward detecting illegal transactions on bitcoin using machine-learning methods. In: Zheng, Z., Dai, H.-N., Tang, M., Chen, X. (eds.) BlockSys 2019. CCIS, vol. 1156, pp. 520–533. Springer, Singapore (2020). https://doi.org/10.1007/978-981-15-2777-7_42
Lo, W.W., Kulatilleke, G.K., Sarhan, M., Layeghy, S., Portmann, M.: Inspection-l: self-supervised GNN node embeddings for money laundering detection in bitcoin. Appl. Intell. 53, 1–12 (2023). https://doi.org/10.1007/s10489-023-04504-9
Lou, Y., Zhang, Y., Chen, S.: Ponzi contracts detection based on improved convolutional neural network. In: 2020 IEEE International Conference on Services Computing (SCC), pp. 353–360 (2020). https://doi.org/10.1109/SCC49832.2020.00053
Montgomery, D.C., Peck, E.A., Vining, G.G.: Introduction to Linear Regression Analysis. Wiley, Hoboken (2021)
Nan, L., Tao, D.: Bitcoin mixing detection using deep autoencoder. In: 2018 IEEE Third International Conference on Data Science in Cyberspace (DSC), pp. 280–287. IEEE (2018)
Perozzi, B., Al-Rfou, R., Skiena, S.: Deepwalk: online learning of social representations. In: Proceedings of the 20th ACM SIGKDD International Conference on Knowledge Discovery and Data Mining, pp. 701–710 (2014)
Samantha Tharani, J., R.K., Muthukkumarasamy, V.: A framework for user-centric visualisation of blockchain transactions in critical infrastructure (2023)
Shojaeenasab, A., Motamed, A.P., Bahrak, B.: Mixing detection on bitcoin transactions using statistical patterns. ar**v preprint ar**v:2204.02019 (2022)
Tang, J., Qu, M., Wang, M., Zhang, M., Yan, J., Mei, Q.: Line: large-scale information network embedding. In: Proceedings of the 24th International Conference on World Wide Web, pp. 1067–1077 (2015)
Veličković, P., Cucurull, G., Casanova, A., Romero, A., Liò, P., Bengio, Y.: Graph attention networks (2018)
Weber, M., et al.: Anti-money laundering in bitcoin: experimenting with graph convolutional networks for financial forensics. ar**v preprint ar**v:1908.02591 (2019)
Wu, J., Liu, J., Chen, W., Huang, H., Zheng, Z., Zhang, Y.: Detecting mixing services via mining bitcoin transaction network with hybrid motifs. IEEE Trans. Syst. Man Cybern. Syst. 52(4), 2237–2249 (2021)
Yu, S., **, J., **e, Y., Shen, J., Xuan, Q.: Ponzi scheme detection in ethereum transaction network. In: Dai, H.-N., Liu, X., Luo, D.X., **ao, J., Chen, X. (eds.) BlockSys 2021. CCIS, vol. 1490, pp. 175–186. Springer, Singapore (2021). https://doi.org/10.1007/978-981-16-7993-3_14
Author information
Authors and Affiliations
Corresponding authors
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2024 The Author(s), under exclusive license to Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Jeyakumar, S.T., Eugene Yugarajah, A.C., Hóu, Z., Muthukkumarasamy, V. (2024). Detecting Malicious Blockchain Transactions Using Graph Neural Networks. In: Dong, N., Pillai, B., Bai, G., Utting, M. (eds) Distributed Ledger Technology. SDLT 2023. Communications in Computer and Information Science, vol 1975. Springer, Singapore. https://doi.org/10.1007/978-981-97-0006-6_4
Download citation
DOI: https://doi.org/10.1007/978-981-97-0006-6_4
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-97-0005-9
Online ISBN: 978-981-97-0006-6
eBook Packages: Computer ScienceComputer Science (R0)