Abstract
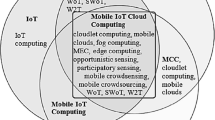
Cloud computing and the Internet of things (IoT) are two diverse technologies having complimentary relationship. The IoT generates massive amounts of data, and cloud computing provides a pathway for that data to travel to its destination. In the modern era, by integrating cloud computing and the Internet of things, a new paradigm has been introduced, i.e., cloud of Things. Cloud-based Internet of Things or cloud of things arose as a platform for intelligent use of applications, information in a cost-effective manner. Both technologies help to raise efficiency in the future. But the integration of these two technologies is challenging and bears some key issues. Therefore, this paper provides a brief investigation of cloud of things concept. In this paper, we review the literature about integration, to analyze and discuss the need behind integration in various applications. In the end, we identify some of the issues and challenges for future work in this promising.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Stergiou, C., Psannis, K.E., Kim, B.G., Gupta, B.: Secure integration of IoT and cloud computing. Futur. Gener. Comput. Syst. 78, 964–975 (2016)
Banerjee, M., Lee, J., Choo, K.K.R.: A blockchain future to Internet of Things security: a position paper. Dig. Commun. Netw. 217–222 (2017)
Gubbi, J., Buyya, R., Marusic, S., Palaniswami, M.: Internet of Things (IoT): a vision, architectural elements, applications and future directions. Futur. Gener. Comput. Syst. 29(7), 1645–1660 (2013)
Cook, A., Robinson, M., Ferrag, M.A., Maglaras, L.A., He, Y., Jones, K., Janicke, H.: Internet of cloud: classification security and privacy issues. In: Cloud Computing for Optimization: Foundations, Applications, and Challenges, pp. 271–301. Springer, Berlin (2018)
Farooq, M.U., Waseem, M., Khairi, A., Mazhar, S.: A critical analysis on the security concerns of internet of things (IoT). Int. J. Comput. Appl. 111–117 (2018)
Agrawal, N., Tapaswi, S.: A lightweight approach to detect the low/high rate IP spoofed cloud DDoS attacks. In: IEEE 7th International Symposium on Cloud and Service Computing (SC2), pp. 118–123 (2017)
Wang, W., Xu, P., Yang, L.T.: Secure data collection, storage and access in cloud-assisted IoT. IEEE Cloud Comput. 77–88 (2018)
**ao, L., Wan, X., Lu, X., Zhang, Y., Wu, D.: IoT security techniques based on machine learning, pp. 277–284 (2018)
Zhou, W., Jia, Y., Peng, A., Zhang, Y., Liu, P.: The effect of IoT new features on security and privacy: new threats, existing solutions, and challenges yet to be solved. IEEE Internet of Things J. 367–384 (2018)
Stergiou, C., Psannis, K.E., Kim, B.G., Gupta, B.: Secure integration of IoT and cloud computing. Futur. Gener. Comput. Syst. 78, 964–975 (2018)
Vorakulpipat, C., Rattanalerdnusorn, E., Thaenkaew, P., Hai, H.D.: Recent challenges, trends, and concerns related to IoT security: an evolutionary study. In: IEEE 20th International Conference on Advanced Communication Technology (ICACT), pp. 405–410 (2018)
Bojović, P.D., Bašičević, I., Ocovaj, S., Popović, M.: A practical approach to detection of distributed denial-of-service attacks using a hybrid detection method. Comput. Electr. Eng. 73, 84–96 (2019)
Wani, A.R., Rana, Q.P., Saxena, U., Pandey, N.: Analysis and detection of DDoS attacks on cloud computing environment using machine learning techniques. In: IEEE Amity International Conference on Artificial Intelligence (AICAI), pp. 870–875 (2019)
Shafi, Q., Basit, A.: DDoS botnet prevention using blockchain in software defined Internet of Things. In: IEEE 16th International Bhurban Conference on Applied Sciences and Technology (IBCAST), pp. 624–628 (2019)
Rebbah, M., Rebbah, D.E.H., Smail, O.: Intrusion detection in cloud Internet of Things environment. In: IEEE 2017 International Conference on Mathematics and Information Technology (ICMIT), pp. 65–70 (2019)
Deogirikar, J., Vidhate, A.: Security attacks in IoT: a survey. In: IEEE International Conference on I-SMAC (IoT in Social, Mobile, Analytics and Cloud) (I-SMAC), 2017, pp. 32–37
Aldaej, A.: Enhancing cyber security in modern Internet of Things using intrusion prevention algorithm for IoT. IEEE Access 964–975 (2018)
Deng, L., Li, D., Yao, X., Cox, D., Wang, H.: Mobile network intrusion detection for IoT system based on transfer learning algorithm. Cluster Comput. 1–16 (2018)
Moon, J., Cho, S., Kum, S., Lee, S.: Cloud-edge collaboration framework for IoT data analytics. In: International Conference on Information and Communication Technology Convergence (ICTC), Oct 2018, pp. 1414–1416. IEEE (2018)
Bhardwaj, A., Sharma, A., Mangat, V., Kumar, K., Vig, R.: Experimental analysis of DDoS attacks on OpenStack cloud platform. In: Proceedings of 2nd International Conference on Communication, Computing and Networking, pp. 3–13 (2019)
Khan, A.N., Fan, M.Y., Malik, A., Memon, R.A.: Learning from privacy preserved encrypted data on cloud through supervised and unsupervised machine learning. In: IEEE 2019 2nd International Conference on Computing, Mathematics and Engineering Technologies (iCoMET), pp. 1–5 (2019)
Dutta, I.K., Ghosh, B., Bayoumi, M.: Lightweight cryptography for Internet of Insecure Things: a survey. In: IEEE 9th Annual Computing and Communication Workshop and Conference (CCWC), pp. 0475–0481 (2019)
Taher, K.A., Jisan, B.M.Y., Rahman, M.M.: Network intrusion detection using supervised machine learning technique with feature selection. In: IEEE International Conference on Robotics, Electrical and Signal Processing Techniques (ICREST), pp. 643–646 (2019)
Hossain, M.M., Fotouhi, M., Hasan, R.: Towards an analysis of security issues, challenges, and open problems in the internet of things. IEEE World Congress on Services, pp. 21–28 (2015)
Goyal, T., Rathi, R., Jain, V.K., Pilli, E.S., Mazumdar, A.P.: Big data handling over cloud for internet of things. Int. J. Inf. Technol. Web Eng. (IJITWE) 13(2), 37–47 (2018)
Xu, S., Yang, G., Mu, Y., Liu, X.: A secure IoT cloud storage system with fine-grained access control and decryption key exposure resistance. Futur. Gener. Comput. Syst. 167–175 (2018)
Khan, M.A., Salah, K.: IoT security: review, blockchain solutions, and open challenges. Futur. Gener. Comput. Syst. 82, 395–411 (2018)
Shen, S., Huang, L., Zhou, H., Yu, S., Fan, E., Cao, Q.: Multistage signaling game-based optimal detection strategies for suppressing malware diffusion in fog-cloud-based IoT networks. IEEE Internet of Things J. 1043–1054 (2018)
Adat, V., Gupta, B.B.: Security in Internet of Things: issues, challenges, taxonomy, and architecture. Telecommunication Systems 67(3), 423–441 (2018)
John, J., Norman, J.: Major vulnerabilities and their prevention methods in cloud computing. In: Advances in Big Data and Cloud Computing, pp. 11–26. Springer, Singapore (2018)
Al-Garadi, M.A., Mohamed, A., Al-Ali, A., Du, X., Guizani, M.: A survey of machine and deep learning methods for internet of things (IoT) security (2018)
Aldaej, A.: Enhancing cyber security in modern Internet of things (IoT) using intrusion prevention algorithm for IoT (IPAI). IEEE Access (2019)
Li, Z., Yang, Z., **e, S.: Computing resource trading for edge-cloud-assisted Internet of Things. IEEE Trans. Ind. Inform. (2019)
Li, X., Wang, Q., Lan, X., Chen, X., Zhang, N., Chen, D.: Enhancing cloud-based IoT security through trustworthy cloud service: an integration of security and reputation approach. IEEE Access 7, 9368–9383 (2019)
Kumar, Y., Kaul, S., Sood, K.: Effective use of the machine learning approaches on different clouds. 2019 Available at SSRN 3355203
Safa, N.S., Maple, C., Haghparast, M., Watson, T., Dianati, M.: An opportunistic resource management model to overcome resource‐constraint in the Internet of Things. Concurr. Comput.: Pract. Exp. (2019)
Singla, A., Sharma, A.: Physical access system security of IoT devices using machine learning techniques. 2019. Available at SSRN 3356785
Stergiou, C., Psannis, K.E., Gupta, B.B., Ishibashi, Y.: Security, privacy & efficiency of sustainable Cloud computing for Big Data & IoT. Sustain. Comput.: Inform. Syst. 19, 174–184 (2019)
Wazid, M., Das, A.K., Hussain, R., Succi, G., Rodrigues, J.J.: Authentication in cloud-driven IoT-based big data environment: survey and outlook. J. Syst. Archit. (2019)
Jia, H., Liu, X., Di, X., Qi, H., Cong, L., Li, J., Yang, H.: Security strategy for virtual machine allocation in cloud computing. Procedia Comput. Sci. 147, 140–144 (2019)
Gurulakshmi, K., Nesarani, A.: Analysis of IoT bots against DDOS attack using machine learning algorithm. In: IEEE 2018 2nd International Conference on Trends in Electronics and Informatics (ICOEI), pp. 1052–1057 (2019)
Achbarou, O., El Bouanani, S.: Securing cloud computing from different attacks using intrusion detection systems. IJIMAI 4(3), 61–64 (2019)
Kirichek, R., Kulik, V., Koucheryavy, A.: False clouds for Internet of Things and methods of protection. In: IEEE 2016 18th International Conference on Advanced Communication Technology (ICACT), pp. 201–205 (2019)
Hassan, W.H.: Current research on Internet of Things (IoT) security: a survey. Comput. Netw. 148, 283–294 (2019)
Nawir, M., Amir, A., Yaakob, N., Lynn, O.B.: Internet of Things (IoT): taxonomy of security attacks. In: IEEE 2016 3rd International Conference on Electronic Design (ICED), pp. 321–326 (2019)
Yin, D., Zhang, L., Yang, K.: A DDoS attack detection and mitigation with software-defined Internet of Things framework. IEEE Access 6, 24694–24705 (2019)
Zhang, Y., Li, P., Wang, X.: Intrusion detection for IoT based on improved genetic algorithm and deep belief network. IEEE Access 7, 31711–31722 (2019)
Chaabouni, N., Mosbah, M., Zemmari, A., Sauvignac, C., Faruki, P.: Network intrusion detection for IoT security based on learning techniques. IEEE Commun. Surv. Tutor. (2019)
Li, Z., Rios, A.L.G., Xu, G., Trajković, L.: Machine learning techniques for classifying network anomalies and intrusions. In: IEEE 2019 IEEE International Symposium on Circuits and Systems (ISCAS), pp. 1–5 (2019)
Chapaneri, R., Shah, S.: A comprehensive survey of machine learning-based network intrusion detection. In: Smart Intelligent Computing and Applications, pp. 345–356 (2019)
Praveen, B.V., Mahita, D., Devi, P.R., Sudheshna, A.: Classifying the probe attacks using machine learning techniques in R and Hadoo. Int. J. Appl. Eng. Res. 13(7), 5175–5178 (2017)
Jayasinghe, U., Lee, G.M., Um, T.W., Shi, Q.: Machine learning based trust computational model for IoT services. IEEE Trans. Sustain. Comput. 4(1), 39–52 (2019)
Rath, M., Pati, B.: Security assertion of IoT devices using cloud of things perception. Int. J. Interdiscip. Telecommun. Netw. (IJITN) 11(4), 17–31 (2019)
Distefano, S., Merlino, G., Puliafito, A.: Enabling the cloud of things. In: 2012 Sixth International Conference on Innovative Mobile and Internet Services in Ubiquitous Computing. IEEE (2012)
Aazam, M., Huh, E.N., St-Hilaire, M., Lung, C.H., Lambadaris, I.: Cloud of things: integration of IoT with cloud computing. In: Robots and Sensor Clouds, pp. 77–94. Springer, Berlin (2016)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2021 The Editor(s) (if applicable) and The Author(s), under exclusive license to Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Singh, S., Singh, A., Goyal, V. (2021). Cloud of Things: A Systematic Review on Issues and Challenges in Integration of Cloud Computing and Internet of Things. In: Singh, P.K., Singh, Y., Kolekar, M.H., Kar, A.K., Chhabra, J.K., Sen, A. (eds) Recent Innovations in Computing. ICRIC 2020. Lecture Notes in Electrical Engineering, vol 701. Springer, Singapore. https://doi.org/10.1007/978-981-15-8297-4_46
Download citation
DOI: https://doi.org/10.1007/978-981-15-8297-4_46
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-15-8296-7
Online ISBN: 978-981-15-8297-4
eBook Packages: Computer ScienceComputer Science (R0)