Abstract
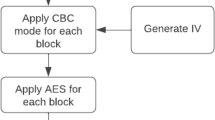
In today’s world, optimization is what needs to be talked about. The explosive growth of the Internet and communication technologies has made the widespread use of images inevitable. The special characteristics of the image, such as high bit rate with limited bandwidth, redundancy, bulk capacity, and correlation between pixels, make standard algorithms unsuitable for image encryption. As cybercrime has reached an all-time high, pre-encryption of data is required for protection. From personal data traded on the dark web to application vulnerabilities, our data is constantly monitored, making encryption paramount. When it comes to encryption, AES (Advanced Encryption Standard) is the gold standard for security. It is a subset of the Rijndael block cipher, which uses a 128-bit data block and a 128-bit, 192-bit and 256-bit key size, giving three different versions of AES, namely AES128, AES192, and AES256. It is a symmetric encryption algorithm that uses the same key for encryption and decryption. The article proposes an algorithm based on a modified AES key extension, in which the encryption process is a bitwise exclusive or an operation of a set of image pixels together with 128-bit key that changes for each set of pixels.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Belyaev, M.A.: Foundations of Computer Science. M.: Triumph Publishing House, 200 (2015)
Cherkesova, L., Korochencev, D., Revyakina, E., Boldyrihin, N., Roshchina, E.: Digitalization of the agro-industrial complex: analysis of existing vulnerabilities in quantum cryptography systems. E3S Web Conf. 175, 05026 (2020)
Razumov, P., Boldyrikhin, N., Cherckesova, L Safaryan, O., Reshetnikova, I., Beryoza, A.: Specific features of the practical implementation of observation planning in systems for monitoring networks with dynamic topology. E3S Web Conf. 224, 01033 (2020)
Zhilin, V.V., Drozdova, I.I., Sakharov, I.A., Safaryan, O.A., Cherckesova, L.V., Porksheyan, V.M., Lobodenko, A.G., Morozov, S.A.: IEEE East-West Design and Test Symposium, EWDTS 2019. Institute of Electrical and Electronics Engineers Inc. 8884375 (2019). https://doi.org/10.1109/EWDTS.2019.8884375
Berlekamp, E.: Algebraic Coding Theory: Textbook. Moscows, Triumph Publishing House, 670 (2012)
Barron, H.C., Auksztulewicz, R., Friston, K.: Prediction and memory: a predictive coding account Progress in Neurobiology, September 2020, vol. 192, 101821 (2020). https://doi.org/10.1016/j.pneurobio.2020.101821
Zhu, J., Shi, H., Song, B., Tao, Y., Tan, S.: Information concentrated variational auto-encoder for quality-related nonlinear process monitoring. J. Process Control 94, 12–25. https://doi.org/10.1016/j.jprocont.2020.08.002
Lavanya, R., Karpagam, M.: Enhancing the security of AES through small scale confusion operations for data communication. Microprocess. Microsyst. 75,(2020). https://doi.org/10.1016/j.micpro.2020.103041
Balreira, D.G., Walter, M., Fellner, D.W.: A survey of the contents in introductory. Comput. Graph. Courses Comput. Graph. 77G:\03.05\V. 77, 88–96. https://doi.org/10.1016/j.cag.2018.10.001
Yang, A., Liu, H., Chen, Y., Zhang, C., Yang, K.: Digital video intrusion intelligent detection method based on narrowband Internet of Things and its application. Image Vis. Comput. 97,(2020). https://doi.org/10.1016/j.imavis.2020.103914
Islam, N., Shahid, Z., Puech, W.: Denoising and error correction in noisy AES-encrypted images using statistical measures. Signal Process. Image Commun. 41, 15–27 (2016)
Mao, V.: Modern Cryptography: Theory and Practice: Moscow, Williams Publishing House, 768 (2015)
Kumar, P., Rana, S.B.: Development of modified AES algorithm for data security. Optik 127(4), 2341–2345 (2016)
Kubota, T., Yoshida, K., Shiozakia, M.: Takeshi Fu**o Deep learning side-channel attack against hardware implementations of AES. Microprocess. Microsyst. 103383 (2020). https://doi.org/10.1016/j.micpro.2020.103383
Ozhiganov, A.A.: Cryptography: Textbook. St. Petersburg: ITMO University, 140 (2016)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2022 The Author(s), under exclusive license to Springer Nature Switzerland AG
About this paper
Cite this paper
Babayan, M., Buglak, A., Gordov, N., Pilipenko, I., Cherckesova, L., Safaryan, O. (2022). Encryption of Images Using the Modified AES Algorithm and Its Comparison with the Original AES. In: Beskopylny, A., Shamtsyan, M. (eds) XIV International Scientific Conference “INTERAGROMASH 2021". Lecture Notes in Networks and Systems, vol 246. Springer, Cham. https://doi.org/10.1007/978-3-030-81619-3_17
Download citation
DOI: https://doi.org/10.1007/978-3-030-81619-3_17
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-81618-6
Online ISBN: 978-3-030-81619-3
eBook Packages: EngineeringEngineering (R0)