Search
Search Results
-
Novel key-integration to safeguard counting-based secret-sharing from possibilities of cyberattack breaches
In the face of malicious cyberattacks, classic security approaches like cryptography and steganography are becoming not sufficient. Secrecy are...
-
Public key based bidirectional shadow image authentication without pixel expansion in image secret sharing
Image secret sharing (ISS) is gaining popularity due to the importance of digital images and its wide application to cloud-based distributed storage...
-
Multi-party codebook distribution strategy based on secret sharing
The paper addresses the issue of secure distribution of codebooks in the field of information security, particularly in the domain of covert...

-
Strengthening wavelet based image steganography using Rubik’s cube segmentation and secret image scrambling
Image steganography is an extremely rich and significant exploration region that gives productive answers to some genuine and modern issues. This...

-
Software and hardware realizations for different designs of chaos-based secret image sharing systems
Secret image sharing (SIS) conveys a secret image to mutually suspicious receivers by sending meaningless shares to the participants, and all shares...

-
Authentic secret share creation techniques using visual cryptography with public key encryption
In the digital transparent world, share the secret messages are challenged one. Visual cryptography (VC) is safer method for information transfer...

-
A reversible data hiding in encrypted image based on additive secret sharing with adaptive bit-plane prediction
With the rapid development of 5G network, protecting multimedia data security has attracted a lot of attentions, and Reversible Data Hiding in...

-
Security to text (S2T): multi-layered based security approaches for secret text content
In the digital world, text data is produced in an unstructured manner across various communication channels. Extracting valuable information from...

-
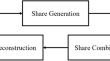
A survey on counting-based secret sharing schemes for resource-constrained environments: techniques, security, challenges, and future directions
Secret sharing schemes play a vital role in securely distributing a secret among multiple participants, ensuring confidentiality and access control....

-
Physical-layer secret key generation based on domain-adversarial training of autoencoder for spatial correlated channels
As a novel approach to enhance information security, physical-layer key generation is based on the channel reciprocity and spatial decorrelation of...

-
Enhanced block based progressive visual secret sharing scheme for grayscale and color image
Block by block, the secret image will be retrieved from user-friendly and noise-like shares in the Block Based Progressive Secret Sharing (BPVSS)...

-
Secret-free security: a survey and tutorial
“Classical keys,” i.e., secret keys stored permanently in digital form in nonvolatile memory, appear indispensable in modern computer security—but...
-
Watermarkable Public Key Encryption with Efficient Extraction Under Standard Assumptions
The current state of the art in watermarked public-key encryption schemes under standard cryptographic assumptions suggests that extracting the...
-
Extraction of secrets from LSB stego images using various denoising methods
Extraction of the secret is the main goal of steganalysis and in order to accomplish it, an apt cover estimator is a viable solution. Also, the...

-
Deep Multi-image Hiding with Random Key
Multi-image hiding is the technique of hiding multiple secret images within one cover image. In most existing methods, it is possible for one...
-
Quantum cryptanalysis of Farfalle and (generalised) key-alternating Feistel networks
Farfalle is a permutation-based construction for building a pseudorandom function which has been proposed by Bertoni et al. in 2017. In this work, we...

-
Steganographic key recovery for adaptive steganography under “known-message attacks”
Since the performance of STC (Syndrome-Trellis Codes) is approaching the theoretical optimum in minimizing embedded distortion, STC-based adaptive...

-
Reversible data hiding based on histogram and prediction error for sharing secret data
With the advancement of communication technology, a large number of data are constantly transmitted through the internet for various purposes, which...

-
LocKey: Location-Based Key Extraction from the WiFi Environment in the User’s Vicinity
We investigate extracting persistent information from semi-volatile signals in the user’s vicinity to extend existing authentication factors. We use...
-

