Search
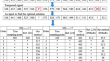
Search Results
-
A replay attack detection scheme based on perceptual image hashing
Perceptual image hashing has mainly been used in the literature to authenticate images or to identify similar contents for image copy detection. In...

-
Image perceptual hashing for content authentication based on Watson’s visual model and LLE
Image perceptual hashing has been widely used in image content authentication. In order to extract hashing sequences that are more consistent with...

-
PIH-mSCM: a modified spiking cortical model for perceptual image hashing and its application to copy detection
For one of the most crucial copyright protection of multimedia content, copy image detection necessitates feature extraction and feature matching....

-
An Image Perceptual Hashing Algorithm Based on Convolutional Neural Networks
The conventional perceptual hashing algorithms are constrained to a singular global feature extraction algorithm and lack efficient scalability...
-
Using Perceptual Hashing for Targeted Content Scanning
The Internet is increasingly used to disseminate unethical and illegal content. A grave concern is child sexual abuse material that is often...
-
FRIH: A face recognition framework using image hashing
Face recognition is one of the most important research topics in computer vision. Indeed, the face is an important means of communication with humans...

-
A novel image hashing with low-rank sparse matrix decomposition and feature distance
Image hashing is an efficient technique of image processing for various applications, such as retrieval, copy detection and authentication. In this...

-
Perceptual hashing scheme using KAZE feature descriptors for combinatorial manipulations
Perceptual image hashing methods utilize the visual phenomenon of the images and produce a fixed-length hash function and this hash value can be...

-
Incremental image retrieval method based on feature perception and deep hashing
How to propose an image retrieval algorithm with adaptable model and wide range of applications for large-scale datasets has become a critical...

-
Perceptual Image Hashing with Bidirectional Generative Adversarial Networks for Copy Detection
The traditional perceptual hashing algorithm is generally achieved by artificially extracting features from an image and quantizing them into a hash...
-
A perceptual entanglement-based image authentication with tamper localisation
With the recent development in image editing tools the content of digital images can be easily manipulated. Research efforts are being deployed to...

-
A review of hashing based image authentication techniques
In the recent digitization era, image hashing is a key technology, including image recognition, authentication and manipulation detection, among many...

-
Attention-based deep supervised hashing for near duplicate video retrieval
With the explosive growth of video data on the Internet, near duplicate video retrieval (NDVR) has become an important and challenging issue in the...

-
Swin transformer-based supervised hashing
With the rapid development of the modern internet, image data are growing explosively. How to retrieve specific images from such big data has become...

-
Perceptual image hashing using transform domain noise resistant local binary pattern
A new Discrete Cosine Transform (DCT) domain Perceptual Image Hashing (PIH) scheme is proposed in this paper. PIH schemes are designed to extract a...

-
An encrypted speech authentication and tampering recovery method based on perceptual hashing
With the progress of speech retrieval technology in the cloud, it brings a lot of conveniences for speech user. Yet, the inquiry encrypted speech...
-
A lightweight robust image hash based on random tensors and angle features for IoT devices
Image hashing can be extensively used in image forensics, and the lightweight image hash suitable for IoT smart devices plays an important role of...

-
A novel hashing-inverted index for secure content-based retrieval with massive encrypted speeches
The content-based speech retrieval scheme using the hash technique boasts high accuracy; however, its index structures, such as the hash table,...

-
Asymmetric hashing based on generative adversarial network
In the era of big data, social media, large-scale video, image, and text data is produced every day. The approximate nearest neighbor (ANN) search...

-
Auto-authentication watermarking scheme based on CNN and perceptual hash function in the wavelet domain
This paper presents a novel method for image watermarking authentication using Convolutional Neural Networks (CNN). The proposed method addresses the...

