Search
Search Results
-
Markov enhanced graph attention network for spammer detection in online social network
Online social networks (OSNs) are an indispensable part of social communication where people connect and share information. Spammers and other...

-
Early prediction of sepsis using a high-order Markov dynamic Bayesian network (HMDBN) classifier
Sepsis is among the leading causes of morbidity, mortality and high costs in the ICU. The early prediction and intervention of sepsis is a...

-
Consistent and Tractable Algorithm for Markov Network Learning
Markov network (MN) structured output classifiers provide a transparent and powerful way to model dependencies between output labels. The MN...
-
Relational attention-based Markov logic network for visual navigation
We argue the agent’s low generalization problem for searching target object in challenging visual navigation could be solved by "how" and "where"...

-
Polyphonic music generation generative adversarial network with Markov decision process
In the process of polyphonic music creation, it is important to combine two or more independent melodies through technical treatment. However, due to...

-
Adaptive Randomized Graph Neural Network Based on Markov Diffusion Kernel
Graph neural networks (GNNs) especially Graph convolutional networks (GCNs) GCNs, are popular in graph representation learning. However, GCNs only...
-
Attention-enabled adaptive Markov graph convolution
GNNs (Graph Neural Networks) have attracted increasing attention for their strong power on dealing with the graph structures. However, it remains a...

-
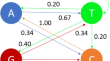
Hidden Markov Model
This chapter first introduces the basic concepts of the Hidden Markov Model, and then describes the probability calculation algorithms, learning...
-
Asynchronous control for 2-D Markov jump cyber-physical systems against aperiodic denial-of-service attacks
This work focuses on the asynchronous controller design for two-dimensional Markov jump cyber-physical systems against denial-of-service attacks....
-
Fake news detection via graph-based Markov chains
Social media platforms have seen a major boom in the past decade. Apart from getting entertained and establishing social connections, the use of...
-
Writer verification using directional morphological features and Markov chains
Much of the information about the writer’s style lies in the directionality of the lines that make up the letters of a word. This information, in...

-
A novel feature selection method via mining Markov blanket
Constraint-based relevant feature selection using the Markov blanket (MB) discovery in Bayesian network (BN) has attracted widespread attention in...

-
Personalized Markov Learning Model in Knowledge Map Space
The personalized learning model is the primary basis for selecting educational resources and the foundation of customized education. Currently, the...
-
Deep Reinforcement Learning and Markov Decision Problem for Task Offloading in Mobile Edge Computing
Mobile Edge Computing (MEC) offers cloud-like capabilities to mobile users, making it an up-and-coming method for advancing the Internet of Things...
-
DRL-HIFA: a dynamic recommendation system with deep reinforcement learning based Hidden Markov Weight Updation and factor analysis
Recommendation Systems have obtained huge attention with notion to assist users in determining their interests by prognosticating their ratings or...

-
Stability analysis and stabilization of semi-Markov jump linear systems with unavailable sojourn-time information
This study addresses the stability and stabilization problems of discrete-time semi-Markov jump linear systems (S-MJLSs) with unavailable...
-
Application of a Neocortex Model to Identify Contextual Anomalies in the Industrial Internet of Things Network Traffic
AbstractThis paper examines the problem of identifying network anomalies when processing data streams in industrial systems. A network anomaly refers...

-
Energy enhancement of routing protocol with hidden Markov model in wireless sensor networks
Energy enhancement is a crucial factor while designing routing models in wireless sensor networks (WSNs). Many energy efficiency routing schemes are...

-
Reinforcement learning-based autonomous attacker to uncover computer network vulnerabilities
In today’s intricate information technology landscape, the escalating complexity of computer networks is accompanied by a myriad of malicious threats...

-
Inverse Problem of Censored Markov Chain: Estimating Markov Chain Parameters from Censored Transition Data
Due to the difficulty of collecting comprehensive data sets (factors include limited GPS coverage and the existence of competitors), most transition...
