Search
Search Results
-
Sublinear Algorithms in T-Interval Dynamic Networks
We consider standard T - interval dynamic networks , under the synchronous timing model and the broadcast CONGEST model. In a T - interval dynamic network ,...

-
Explicit constructions of NMDS self-dual codes
Near maximum distance separable (NMDS) codes are important in finite geometry and coding theory. Self-dual codes are closely related to...
-

-
Extract Implicit Semantic Friends and Their Influences from Bipartite Network for Social Recommendation
Social recommendation often incorporates trusted social links with user-item interactions to enhance rating prediction. Although methods that...

-
Parallel continuous skyline query over high-dimensional data stream windows
Real-time multi-criteria decision-making applications in fields like high-speed algorithmic trading, emergency response, and disaster management have...

-
Vectorial negabent concepts: similarities, differences, and generalizations
In Pasalic et al. (IEEE Trans Inf Theory 69:2702–2712, 2023), and in Anbar and Meidl (Cryptogr Commun 10:235–249, 2018), two different vectorial...
-
Some self-dual codes and isodual codes constructed by matrix product codes
In 2020, Cao et al. proved that any repeated-root constacyclic code is monomially equivalent to a matrix product code of simple-root constacyclic...
-
The NP-hard problem of computing the maximal sample variance over interval data is solvable in almost linear time with a high probability
We consider the algorithm by Ferson et al. (Reliab Comput 11(3):207--233, 2005) designed for solving the NP-hard problem of computing the maximal...
-
Some constacyclic BCH codes with good parameters
BCH codes as a subclass of constacyclic BCH codes have been widely studied, while the results on the parameters of BCH codes over finite fields are...
-
Stagnation Detection in Highly Multimodal Fitness Landscapes
Stagnation detection has been proposed as a mechanism for randomized search heuristics to escape from local optima by automatically increasing the...

-
Security analysis of the ISO standard \(\textsf{OFB}\)-\(\textsf{DRBG}\)
Deterministic random bit generators (DRBGs) are essential tools in modern cryptography for generating secure and unpredictable random numbers. The...

-
A survey of compositional inverses of permutation polynomials over finite fields
In this paper, we survey on the recent results and methods in the study of compositional inverses of permutation polynomials over finite fields. In...
-
Constructions for t-designs and s-resolvable t-designs
The purpose of the present paper is to introduce recursive methods for constructing simple t -designs, s -resolvable t -designs, and large sets of t -desi...
-
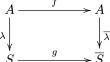
Finding orientations of supersingular elliptic curves and quaternion orders
An oriented supersingular elliptic curve is a curve which is enhanced with the information of an endomorphism. Computing the full endomorphism ring...

-
On the maximum size of variable-length non-overlap** codes
Non-overlap** codes are a set of codewords such that any nontrivial prefix of each codeword is not a nontrivial suffix of any codeword in the set,...

-
Multi-view Heterogeneous Graph Neural Networks for Node Classification
Recently, with graph neural networks (GNNs) becoming a powerful technique for graph representation, many excellent GNN-based models have been...

