Abstract
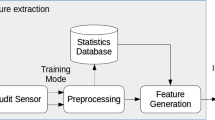
In order to solve the problem of network attack by malicious code using Domain Name System (DNS), on the basis of analyzing the characteristics of malicious code lines and abnormal operation behaviors, this paper proposes an unsupervised abnormal IP detection method based on DNS log data. Through the construction of DNS fingerprint characteristics, it is used to demonstrate the DNS behavior characteristics of IP to the greatest extent. The detection model is constructed by using isolated forest and local outlier factor algorithm, and the anomaly score of IP is obtained. The experimental results show that the detection method designed in the paper can well detect the attack exceptions and operation exceptions in the network environment. With the help of whitelist, the accuracy of the method can reach more than 90% after selecting the appropriate anomaly score threshold.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Lin, C.H., Li, X.D., JJ, et al.: DNS traffic anomaly detection based on w-kmeans algorithm. Comput. Eng. Des. 34(006):2104–2108 (2013)
Wang, Q., **e, K., Ma, Y., et al.: DNS tunnel detection based on log statistics. J. Zhejiang Univ. (Engineering Science edition) 2020(9) (2020)
Wang, J.Y., Shi, J.T., Zhang, Z.X., et al.: Source IP anomaly detection algorithm for DNS request data flow based on relative density. High Technol. Commun. 26(Z2), 849–856 (2016)
Mockapetris, P,, Dunlap, K.J.: Development of the domain name system. ACM SIGCOMM Comput. Commun. Rev. 25(1) (2001)
Li, B.S., Chang, A.Q., Zhang, J.X.: IoT botnets threatened network infrastructure security seriously—analysis of Dyn attacked by Botnet. J. Inf. Secur. Res. 2(11), 1042–1048 (2016)
Wang, J.Y., Shi, J.T., Zhang, Z.X., et al.: An algorithm for detection of source IP anomalies in DNS query based on relative density. Chinese High Technol. Lett. 26(Z2), 849–856 (2016)
Ji, X., Huang, T., Hua, E.X., Sun, L.: A DNS query anomaly detection algorithm based on log information. J. Bei **g Univ. Posts Telecommun. 41(6), 83–89 (2018)
Singh, M., Singh, M., Kaur, S.: Detecting bot-infected machines using DNS fingerprinting. Digit. Investig. 28 (2018)
Lee, J., Lee, H.: GMAD: Graph-based Malware Activity Detection by DNS traffic analysis. Comput. Commun. 49(Aug.1), 33–47 (2014)
Gu, Y.H., Guo, Z.Y.: Fast-flux botnet domain detection method based on network Traffic. J. Inf. Secur. Res. 006(005), 388–395 (2020)
Woodbridge, J., Anderson, H.S., Ahuja, A., et al.: Predicting domain generation algorithms with long short-term memory networks. ar**v: 1611.00791 [cs], (2016)
Breunig, M.M., Kriegel, H.P., Ng. R.T., et al.: LOF:Identifying density-based local outliers. In: Proceedings of ACM SIGMOD Conference, pp. 427-438. ACM, New York (2000)
Liu, F.T., Ting, K.M., Zhou, Z.H.: Isolation forest. In: 2008 Eighth IEEE International Conference on Data Mining (2009)
Chandola, V., Banerjee, A., Kumar, V.: Anomaly Detection: A Survey. ACM Comput. Surv. 41(3) (2009)
Antonakakis, M., Perdisci, R., Nadji, Y., et al.: From throw-away traffic to bots: detecting the rise of DGA-based malware. In: Usenix Conference on Security Symposium (2012)
Wang, Q., **e, K., Ma, Y., et al.: Detection of DNS tunnels based on log statistics feature. J. Zhejiang Univ. (Engineering Science), 54(9) (2020)
Buczak, A.L., Hanke, P.A., Cancro, G.J., et al.: Detection of tunnels in PCAP data by random Forests cyber In: Cyber and Information Security Research (CISR) Conference (2016)
Zuo, X.J., Dong, L.M., Qu, W.: Fast-flux botnet detection method based on domain name system traffic. Comput. Eng. 43(09), 185–193 (2017)
Funding Statement
This work was supported by the National Natural Science Foundation of China (NSFC) under Grant No. 61901447.
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2023 The Author(s), under exclusive license to Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Jiarong, W., Zhongtian, L., Fazhi, Q., Tian, Y., Jiahao, L., Caiqiu, Z. (2023). Unsupervised Anomaly Detection Method Based on DNS Log Data. In: Liang, Q., Wang, W., Mu, J., Liu, X., Na, Z. (eds) Artificial Intelligence in China. AIC 2022. Lecture Notes in Electrical Engineering, vol 871. Springer, Singapore. https://doi.org/10.1007/978-981-99-1256-8_5
Download citation
DOI: https://doi.org/10.1007/978-981-99-1256-8_5
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-99-1255-1
Online ISBN: 978-981-99-1256-8
eBook Packages: Computer ScienceComputer Science (R0)