Abstract
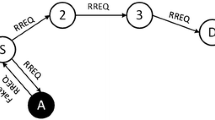
Ad hoc networks are particularly vulnerable as compare to traditional networks mainly due to their lack of infrastructure. A malicious node can easily disrupt both the routing discovery phase and the data forwarding phase of a routing protocol if it is not secured enough. This paper proposes a new secure reactive routing protocol named TRP (Trust-based Routing Protocol) that relies on a distributed trust model managing trust levels. The model provides an estimation of trust level to each route to help a source node to chose the most secure one. Our security mechanism is protected and does not affect significantly the network performance.
Chapter PDF
Similar content being viewed by others
References
Asokan, N. and Ginzboorg, Philip (2000). Key-agreement in ad-hoc networks. Computer Communications, 23(17): 1627–1637.
Beth, T., Borcherding, M., and Klein, B. (1994). Valuation of trust in open networks. In Proc. 3rd European Symposium on Research in Computer Security — ESORICS’ 94, pages 3–18.
B.K.R. Yahalom and T. Beth (1994). Trust relationships in secure systems-a distributed authentication perspective. Computer Systems, 7(1):45–73.
Buchegger, Sonja and Boudec, Jean-Yves Le (2002). Cooperative Routing in Mobile Ad-hoc Networks: Current Efforts Against Malice and Selfishness. In Lecture Notes on Informatics, Mobile Internet Workshop, Informatik 2002, Dortmund, Germany. Springer.
J.P. Hubaux, L. Buttyan, and S. Capkun (2001). The quest for security in mobile ad hoc networks. In Proceedings of ACM Symposium on Mobile Ad Hoc Networking and Computing (MobiHOC 2001), Long Beach, CA, USA.
Lakshmi, Venkatraman (2001). Secured routing protocol for ad hoc networks. Master thesis, University of Cincinnati, Computer Science.
Marti, S, Giuli, T, Lai, K, and Baker, M (2000). Mitigating routing misbehavior in mobile ad hoc networks. Proceedings of MOBICOM.
Michiardi, Pietro and Molva, Refik (2002). Core: A COllaborative REputation mechanism to enforce node cooperation in mobile ad hoc networks. In Communication and Multimedia Security 2002 Conference.
Papadimitratos, Panagiotis and J.Haas, Zygmunt (2002). Secure routing for mobile ad hoc networks. Proceedings of the SCS Communication Networks and Distributed Systems Modeling and Simulation Conference.
P. Papadimitratos and Z.J. Haas (2003). Secure data transmission in mobile ad hoc networks. In Proceedings of the 2003 ACM workshop on Wireless security table of contents, pages 41–50.
Zhou, Lidong and Haas, Zygmunt J. (1999). Securing ad hoc networks. IEEE Network, 13(6):24–30.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2005 International Federation for Information Processing
About this paper
Cite this paper
Xue, X., Leneutre, J., Ben-Othman, J. (2005). A Trust-Based Routing Protocol for Ad Hoc Networks. In: Belding-Royer, E.M., Al Agha, K., Pujolle, G. (eds) Mobile and Wireless Communication Networks. MWCN 2004. IFIP International Federation for Information Processing, vol 162. Springer, Boston, MA. https://doi.org/10.1007/0-387-23150-1_22
Download citation
DOI: https://doi.org/10.1007/0-387-23150-1_22
Publisher Name: Springer, Boston, MA
Print ISBN: 978-0-387-23148-8
Online ISBN: 978-0-387-23150-1
eBook Packages: Computer ScienceComputer Science (R0)