Abstract
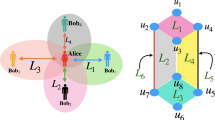
Asymmetric entanglement could provide a crucial layered key structure for quantum cryptography. A new symmetrical tripartite quantum key distribution scheme based on the simplest layered quantum key distribution (L-QKD) model is devised. With an interesting rotational symmetrical key distribution scheme, the proposed tripartite QKD protocol could establish a more integrated key system, which expands the number of conference keys for secure broadcast and distribute layered secret keys among any legitimate participants simultaneously. The proposed scheme is more flexible, robust and efficient to guarantee the fairness among communication parties than the original L-QKD protocol, and our scheme also could be applied to encryption in the butterfly network precisely. Moreover, based on three asymmetric (4, 4, 2) entangled state, a novel symmetric (4, 4, 4) entangled state to implement L-QKD scheme is discussed. Finally, the security of L-QKD scheme is analyzed via information-theoretic proof.




Similar content being viewed by others
References
Gisin, N., Ribordy, G., Tittel, W., Zbinden, H.: Quantum cryptography. Rev. Mod. Phys. 74, 145 (2002)
Wootters, W.K., Zurek, W.H.: A single quantum cannot be cloned. Nature. 299, 802 (1982)
Coffman, V., Kundu, J., Wootters, W.K.: Distributed entanglement. Phys. Rev. A. 61, 052306 (2000)
Bennett, C. H., Brassard, G.: Quantum cryptography: Public key distribution and coin tossing. Proceedings of IEEE International Conference on Computers. Systems and Signal Processing. Bangalore, India, 175–179 (1984)
Ekert, A.K.: Quantum cryptography based on Bell’s theorem. Phys. Rev. Lett. 67, 661 (1991)
Ep**, M., Kampermann, H., Bruß, D.: Multi-partite entanglement can speed up quantum key distribution in networks. New J. Phys. 19, 093012 (2017)
Scarani, V., Bechmann, P.H., Cerf, N.J.: The security of practical quantum key distribution. Rev. Mod. Phys. 81, 1301 (2009)
Mayers, D.: Unconditional security in quantum cryptography. J. ACM. 48, 351 (2001)
Greenberger, D.M., Horne, M.A., Shimony, A., Zeilinger, A.: Bell’s theorem without inequalities. Am. J. Phys. 58, 1131 (1990)
Schön, C., Solano, E., Verstraete, F.: Sequential generation of entangled multiqubit states. Phys. Rev. Lett. 95, 110503 (2005)
Huang, P., Huang, J., Zhang, Zeng, G.H.: Quantum key distribution using basis encoding of Gaussian-modulated coherent states. Phys. Rev. A. 97, 042311 (2018)
Acín, A., Cirac, J.I., Lewenstein, M.: Entanglement percolation in quantum networks. Nat. Phys. 3, 256 (2007)
Luo, M.X.: Computationally efficient nonlinear bell inequalities for quantum networks. Phys. Rev. Lett. 120, 140402 (2018)
Yang, Y., Yang, J., Zhou, Y., Shi, W., Chen, X.: Quantum network communication: a discrete-time quantum-walk approach. Science China Inf. Sci. 61, 042501 (2018)
Leung, D., Oppenheim, J., Winter, A.: Quantum network communication—the butterfly and beyond. IEEE Trans. Inf. Theory. 56, 3478 (2010)
Bechmann, P.H., Tittel, W.: Quantum cryptography using larger alphabets. Phys. Rev. A. 61, 062308 (2000)
Cerf, N.J., Bourennane, M., Karlsson, A., Gisin, N.: Security of quantum key distribution using d-level systems. Phys. Rev. Lett. 88, 127902 (2002)
Pivoluska, M., Huber, M., Malik, M.: Layered quantum key distribution. Phys. Rev. A. 97, 032312 (2018)
Wang, X.B.: Quantum key distribution with two-qubit quantum codes. Phys. Rev. Lett. 92, 077902 (2004)
**u, X.M., Li, Q.Y., Lin, Y.F., Dong, H.K., Dong, L., Gao, Y.J.: Preparation of four-photon polarization-entangled decoherence-free states employing weak cross-Kerr nonlinearities. Phys. Rev. A. 94, 042321 (2016)
Erhard, M., Malik, M., Krenn, M., Zeilinger, A.: Experimental GHZ entanglement beyond qubits. ar**v. 1708, 03881 (2017)
Hiesmayr, B.C., De Dood, M.J.A., Löffler, W.: Observation of four-photon orbital angular momentum entanglement. Phys. Rev. Lett. 116, 073601 (2016)
Malik, M., Erhard, M., Huber, M.: Multi-photon entanglement in high dimensions. Nat. Photonics. 10, 248 (2016)
Huber, M., de Vicente, J.I.: Structure of multidimensional entanglement in multipartite systems. Phys. Rev. Lett. 110, 030501 (2013)
Ahlswede, R., Cai, N., Li, S.Y., Yeung, R.W.: Network information flow. IEEE Trans. Inf. Theory. 46, 1204 (2000)
Ep**, M., Kampermann, H., Bruss, D.: Robust entanglement distribution via quantum network coding. New J. Phys. 18, 103052 (2016)
Li, D., Gao, F., Qin, S., Wen, Q.: Perfect quantum multiple-unicast network coding protocol. Quantum Inf. Process. 17, 13 (2018)
Bechmann-Pasquinucci, H., Gisin, N.: Incoherent and coherent eavesdrop** in the six-state protocol of quantum cryptography. Phys. Rev. A. 59, 4238 (1999)
Renner, R., Gisin, N., Kraus, B.: Information-theoretic security proof for quantum-key-distribution protocols. Phys. Rev. A. 72, 012332 (2005)
Li, C.Y., Zhou, H.Y., Wang, Y.: Secure quantum key distribution network with bell states and local unitary operations. Chin. Phys. Lett. 22, 1049 (2005)
Lo, H.K., Ma, X., Chen, K.: Decoy state quantum key distribution. Phys. Rev. Lett. 94, 230504 (2005)
Lucamarini, M., Patel, K.A., Dynes, J.F.: Efficient decoy-state quantum key distribution with quantified security. Opt. Express. 21, 24550 (2013)
**u, X.M., Dong, L., Gao, Y.J.: Secure four-site distribution and quantum communication of χ− type entangled states. Opt. Commun. 284, 2065–2069 (2011)
Li, X.H., Deng, F.G., Zhou, H.Y.: Improving the security of secure direct communication based on the secret transmitting order of particles. Phys. Rev. A. 74, 054302 (2006)
Cai, Q.Y.: Eavesdrop** on the two-way quantum communication protocols with invisible photons. Phys. Lett. A. 351, 23–25 (2006)
Zhou, N.R., Zhu, K.N., Zou, X.F.: Multi-party semi-quantum key distribution protocol with four-particle cluster state. Ann. Phys. 531, 1970031 (2019)
Liao, L., Peng, X., Shi, J., Guo, Y.: Graph state-based quantum group authentication scheme. J. Phys. Soc. Jpn. 86, 024403 (2017)
Wang, X.W., **a, L.X., Wang, Z.Y., Zhang, D.Y.: Hierarchical quantum-information splitting. Opt. Commun. 283, 1196–1199 (2010)
Chai, G., Cao, Z.W., Liu, W.Q., Wang, S.Y., Huang, P., Zeng, G.H.: Parameter estimation of atmospheric continuous-variable quantum key distribution. Phys. Rev. A. 99, 032326 (2019)
Acknowledgements
The authors would like to thank the anonymous reviewers for their valuable comments and suggestions that help improve the quality of this manuscript. This work is supported by the National Natural Science Foundation of China (Grant Nos. 61871205 and 61561033), the China Scholarship Council (Grant No. 201606825042), the Major Academic Discipline and Technical Leader of Jiangxi Province (Grant No. 20162BCB22011), and the Natural Science Foundation of Jiangxi Province (Grant No. 20171BAB202002).
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher’s Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Zhang, XH., Yan, XY., Wang, YQ. et al. Tripartite Layered Quantum Key Distribution Scheme with a Symmetrical Key Structure. Int J Theor Phys 59, 562–573 (2020). https://doi.org/10.1007/s10773-019-04349-4
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10773-019-04349-4